ISO 27001 Certification Requirements in the UK (2026 guide)
This guide explains ISO 27001 certification requirements in the UK, covering clauses, Annex A controls, audit process, documentation checklist, and more.
Key takeaways
ISO 27001 certification succeeds when you understand clauses, controls and evidence - not just policies or security tools.
Auditors assess real implementation, documented evidence and ongoing improvement, not intentions or one-off preparation before audit.
Credible certification means accredited certification, structured internal reviews and consistent ISMS maintenance after certification.
In the UK and Europe this typically means UKAS-accredited certification, or certification from another certification body accredited by another reputable IAF accreditation body.
Most ISO 27001 projects fail before the audit even begins - not because security is weak, but because the requirements are misunderstood.
If you are a UK or European SME, SaaS company, professional services firm, or supplier bidding for contracts, this guide is for you. It is written from an auditor’s perspective and explains what certification bodies actually assess during a UKAS-accredited audit, or an audit accredited by another IAF-accredited certification body.
We will walk through the ISO 27001 requirements clause by clause, explain how Annex A controls fit in, outline internal audit expectations, and clarify what documentation is mandatory.
Just as importantly, we will separate 3 things that are often confused: requirements, controls, and certification.
What ISO 27001 is and why UK and European organisations adopt it?
ISO/IEC 27001 is the international standard for information security management. It was developed by the International Organisation for Standardisation (ISO) and the International Electrotechnical Commission (IEC).
The current version, ISO/IEC 27001:2022, sets out how organisations must establish, implement, maintain and continually improve an Information Security Management System (ISMS).
In the UK and European market, ISO 27001 often goes beyond best practice. It provides client assurance during procurement, strengthens supplier onboarding, and supports alignment with GDPR and contractual data protection obligations.
Although it is a voluntary standard, many UK and European organisations find it commercially mandatory when bidding for contracts or entering regulated supply chains.
What are the ISO 27001 certification requirements?
Under ISO/IEC 27001, the certification requirements are defined in Clauses 4-10 of the standard. These clauses are mandatory.
If an organisation wants certification, every requirement within the clauses must be met.
What the clauses are designed to do
Clauses 4–10 set the foundation of your ISMS. They require you to:
Understand your organisational context and risks
Demonstrate leadership and management accountability
Plan how risks will be treated
Provide resources, competence and awareness
Operate the ISMS in a controlled way
Monitor, measure and improve performance
In practice, they ensure your ISMS is structured, risk-based and actively managed.
Requirements vs controls: A common misunderstanding
A frequent mistake is treating Annex A as the certification requirement. It is not.
Annex A contains controls that support risk treatment
The clauses, on the other hand, define the mandatory framework. Without meeting Clauses 4-10, certification is not possible, regardless of how many controls are implemented.
Overview of the ISO 27001 clause structure
ISO/IEC 27001 is structured into 10 clauses. However, not all of them contain audit requirements.
Clauses 0-3: Context and background - Clauses 0-3 provide introduction, scope, normative references and key terms. These sections explain how the standard works and how it should be interpreted. They are not requirements
Clauses 4-10: Mandatory ISMS requirements - The ISO 27001 ISMS requirements are defined in Clauses 4–10. These clauses form the certifiable core of the standard, and are requirements.
Why evidence matters more than intent
In practice, auditors do not just assess what an organisation plans to do. They assess what is operating.
Policies without implementation, risk assessments without action, or processes without records will not satisfy certification requirements. Evidence, in the form of documented information and operating records, is what demonstrates compliance.
Clause-by-clause ISO 27001 requirements explained

Clause 4 - Context of the organisation
Clause 4 requires you to define the foundation of your ISMS.
This includes:
1. Defining the ISMS scope
The scope must clearly state what parts of the business are included. It should define locations, services, systems and boundaries.
Scope errors are among the most common reasons for audit delays or failures. If the scope is vague, artificially narrow, or inconsistent with actual operations, auditors will challenge it.
2. Internal and external issues
Organisations must consider business model, technology, regulatory landscape, supplier dependencies and market pressures. This ensures the ISMS reflects reality rather than theory.
3. Interested parties
You must identify relevant stakeholders, such as customers, regulators, partners and employees, and understand their information security expectations.
4. ISO 27001 legal requirements
Legal, regulatory and contractual obligations relevant to information security must be identified and considered - typically in a legal register spreadsheet. In the UK or Europe, this commonly includes:
GDPR requirements
Data processing agreements
Client security clauses in contracts
These obligations feed directly into the risk assessment and influence control selection. If legal risks are not reflected in your risk treatment decisions, auditors will question the effectiveness of your planning.
Clause 5 - Leadership and commitment
Clause 5 places accountability firmly with top management.
It requires:
Demonstrable leadership commitment
An approved Information Security Policy
Clear assignment of roles and responsibilities
Auditors expect to see evidence that leadership is actively engaged. This may include:
Signed policy approval
Defined ISMS roles
Participation in management reviews
Participation in opening and closing meetings of Stage and Stage 2 audits
Resource allocation decisions
Clause 6 - Planning
Clause 6 introduces the risk-based core of ISO 27001.
Organisations must define:
A risk assessment methodology
A consistent risk treatment approach
Measurable information security objectives
The methodology must explain how risks are identified, analysed and evaluated. It must be repeatable and applied consistently.
The Statement of Applicability (SoA) links risk assessment outcomes to selected Annex A controls. It must justify the inclusion or exclusion of controls and reflect actual risk decisions.
Without a clear link between risk assessment and the SoA, certification readiness is weak.
Clause 7 - Support
Clause 7 focuses on enabling the ISMS to function properly.
It covers:
Adequate resources
Competence and training
Awareness of information security responsibilities
Internal communication
Document control requirements
Auditors assess whether people understand their security responsibilities and whether documentation is controlled, versioned and accessible.
Policies must not only exist; they must be communicated and understood.
Clause 8 - Operation
Clause 8 requires organisations to operate the ISMS in practice.
This includes:
1. ISO 27001 data protection requirements
ISO 27001 does not contain a standalone “data protection clause”. Instead, data protection is addressed through risk treatment decisions and Annex A controls, such as:
Access control
Encryption
Secure data handling
The standard supports compliance with UK GDPR by embedding risk-based security management. However, ISO 27001 certification does not replace legal obligations under data protection law.
Organisations should avoid presenting ISO 27001 as a substitute for regulatory compliance.
2. ISO 27001 backup requirements
Under operational controls, backup arrangements must reflect identified risks.
This includes:
Backup processes
Restoration testing
Defined retention periods
Clear assignment of responsibility
ISO 27001 does not mandate specific backup tools, but requires evidence-based backup controls where risks justify them.
Auditors will request evidence of successful restoration testing, not just policy statements.
3. ISO 27001 business continuity requirements
Business continuity and disaster recovery planning must align with risk assessment outcomes and availability objectives.
Controls relating to continuity are selected through the risk treatment process. While ISO 27001 addresses resilience, organisations with more complex continuity needs may align their approach with ISO 22301 for business continuity management.
The key audit question is simple: are continuity arrangements proportionate to identified risks?
Clause 9 - Performance evaluation
Clause 9 ensures the ISMS is monitored and reviewed.
It requires:
Monitoring and measurement
Defined KPIs
Internal audits
Management reviews
Internal audits must be planned and conducted at defined intervals. They must assess conformity and effectiveness. The results of those audits should then feed into formal management reviews, where leadership evaluates overall ISMS performance, emerging risks, security objectives, audit findings and any required improvement actions.
Accredited certification bodies will also conduct annual surveillance audits. Evidence of ongoing monitoring is therefore essential.
Clause 10 - Improvement
Clause 10 focuses on addressing weaknesses and driving continual improvement.
It requires:
Identification of nonconformities
Corrective action processes
Evidence of continual improvement
Auditors will examine how nonconformities are identified, investigated and resolved, paying close attention to whether root causes have been properly analysed. In accredited audits, repeated issues without clear root-cause analysis or effective corrective action are common findings.
Continual improvement does not mean achieving perfection. Instead, it requires clear evidence that the organisation learns from issues, takes structured corrective action and strengthens the ISMS over time.
Get ISO 27001 certified with confidence
If you are ready to move forward with ISO 27001, we can help. At Tempo Audits, we are a UKAS-accredited certification body built for modern tech companies. We understand SaaS, cloud systems and how fast-moving teams work.
You will work directly with experienced auditors who give clear guidance, honest feedback and a smooth audit process. Get a free quote today.
Annex A controls - How they relate to certification
Annex A is mandatory to consider, but it is not mandatory to implement in full. The 2022 version contains 93 controls, grouped into 4 domains:
Organisational – Governance, policies and supplier security
People – Screening, awareness and disciplinary processes
Physical – Premises and environmental protection
Technological – Access control, encryption and system security
Annex A draws from ISO/IEC 27002 and acts as the reference list for your Statement of Applicability (SoA).
Controls are selected based on risk. For example,
A cloud-native SaaS company may justify physical data centre controls as not applicable if it does not operate infrastructure.
A business with no mobile workforce may treat mobile device controls as low relevance.
A startup with no contractors may have limited supplier-related controls initially.
During audits, certification bodies check that all 93 controls were considered, that exclusions are justified, and that selected controls operate effectively.
Mandatory ISO 27001 documentation checklist
The following documents are non-negotiable for ISO 27001 certification. Without them, certification is not possible.
Core ISMS documentation
☐ ISMS scope statement
Defines boundaries and applicability
Clarifies what is included and excluded
☐ Information security policy
Approved by senior management
Sets overall direction and commitment
☐ Risk assessment methodology
Defines how risks are identified, analysed and evaluated
Includes risk acceptance criteria
☐ Risk assessment (Current version)
Identified assets, threats and vulnerabilities
Risk ratings and risk owners
☐ Risk treatment plan
How risks are addressed
Controls selected, responsibilities and timelines
☐ Statement of Applicability (SoA)
Lists all 93 Annex A controls
Applicability decision for each control
Justification for inclusion or exclusion
Implementation status
☐ Information security objectives and metrics
Measurable security objectives
Monitoring approach
Mandatory process records (Evidence of operation)
☐ Internal Audit Programme and Reports
Audit schedule
Audit findings and outcomes
Evidence of follow-up actions
☐ Management review records
Performance evaluation
Audit and incident review
Decisions and resource allocation
☐ Corrective action log
Nonconformities identified
Root cause analysis
Actions taken and effectiveness verification
Supporting policies and procedures
(Required where applicable based on your SoA)
☐ Access control
☐ Asset management
☐ Change management
☐ Backup and recovery
☐ Logging and monitoring
☐ Incident management
☐ Supplier security
☐ Business continuity
☐ Legal and regulatory register
Operational evidence
☐ User access reviews and joiner/leaver records
☐ Training and awareness records
☐ Vulnerability scan and patch records
☐ Backup logs and restoration tests
☐ Change approvals and deployment records
☐ Security event logs and incident records
Certification bodies will not only check that documents exist, but that they are current, controlled and actively used.
ISO 27001 audit process in the UK and Europe
Certification follows a structured, evidence-based process. In the UK or Europe, this typically involves internal audits, a two-stage external audit, and ongoing surveillance by a UKAS-accredited or other accredited certification body
1. Internal audit
Before certification, you must conduct internal audits at planned intervals. These audits assess whether your ISMS conforms to ISO 27001 and whether it operates effectively in practice.
Auditors will expect to see:
A defined internal audit programme
Audit reports with findings
Evidence that issues were addressed
Evidence of the competence of the internal auditor (typically evidence of experience with ISO 27001 or some other ISO 27001 qualification)
Internal audits are not optional preparation exercises. They are mandatory ISO 27001 requirements and form part of the evidence reviewed during certification.
2. Stage 1 audit - Readiness and documentation review
Stage 1 focuses on documentation and overall readiness.
At this stage, auditors review:
ISMS scope
Policies and procedures
Risk assessment and treatment
Statement of Applicability
Internal audit and management review records
The objective is to confirm that the mandatory ISMS framework is in place and that the organisation is prepared for Stage 2. Any gaps identified must be addressed before proceeding.
At Tempo Audits, Stage 1 is conducted remotely by default. The audit plan is shared in advance, including the schedule, key focus areas and requested evidence. Also, where documentation is well organised, much of the review can be conducted asynchronously, reducing disruption.
3. Stage 2 audit - Implementation and evidence testing
Stage 2 tests whether your ISMS works in practice.
This involves:
Evidence sampling
Control testing
Interviews across departments
Review of operational records
The focus shifts from documented intent to real-world implementation. Auditors assess whether controls are operating, risks are managed, and processes are followed consistently.
At the end of Stage 2, nonconformities (if any) are presented immediately, allowing corrective actions to begin without delay.
Working with a UKAS-accredited certification body
In the UK or Europe, organisations seeking recognised ISO 27001 certification use certification bodies accredited by the United Kingdom Accreditation Service (UKAS) or other reputable accreditation bodies, as this ensures independent oversight and broad market acceptance.
UKAS requires certification bodies to demonstrate:
Independence / Impartiality – Auditors cannot consult on the ISMS they certify
Auditor competence – Auditors must be qualified and sector-competent, following a rigorous competence framework
Ongoing surveillance – Annual surveillance audits after certification
Recertification – A full reassessment typically every 3 years
During audits, findings are classified as:
Minor nonconformities – isolated gaps that do not undermine the ISMS.
Major nonconformities – significant failures that prevent certification until resolved.
Certification is granted only once major nonconformities are closed and corrective actions are accepted. This structured approach ensures ISO 27001 certification in the UK is consistent, credible and independently verified.
Typical audit flow
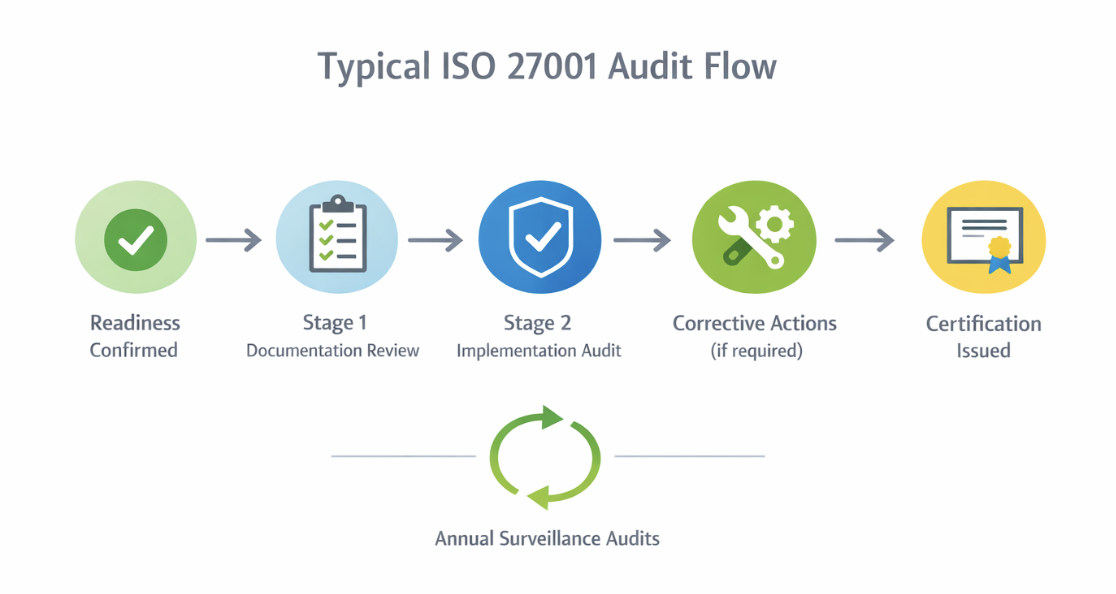
If you are preparing for certification, our pre-audit FAQs provide practical answers to common audit questions and what to expect before Stage 1.
What causes ISO 27001 certification suspension or withdrawal | Maintaining your certification
ISO 27001 certification is not permanent. It can be suspended or withdrawn if the ISMS is no longer maintained or if audit obligations are not met.
The most common cause is major nonconformities during surveillance audits. Examples include:
Failing to update risk assessments,
Not conducting internal audits or management reviews,
Critical controls such as backups not operating, or
Widespread non-compliance with your own policies.
If major issues are not resolved within the agreed timeframe, certification may be withdrawn.
Administrative failures also trigger suspension, such as
Repeatedly postponing audits,
Denying access to evidence, or
Non-payment of certification fees.
Less common but serious causes include fraudulent evidence or misrepresentation.
Therefore, maintaining certification requires ongoing audits, active ISMS management, timely corrective action and open communication with your certification body.
How Tempo Audits supports ISO 27001 readiness
At Tempo Audits, we are built specifically for technology companies. Over 200 organisations, primarily SaaS and cloud-native businesses across Europe, have achieved ISO 27001 certification with us.
We understand how modern tech teams operate, including DevOps workflows, cloud-native infrastructure and continuous deployment environments.
Our founder, Rob Hall, is an experienced tech entrepreneur who created Tempo after seeing how poorly traditional certification bodies served fast-moving technology businesses. We are not a side service within a larger firm. We are a purpose-built, UKAS-accredited certification body that speaks your language.
What this means for you
1. Fast-moving without cutting corners
Stage 1 audits scheduled within days
Reports delivered quickly
Certificates issued promptly once requirements are met
Gaps identified early to avoid late-stage surprises
2. Tech-fluent auditors
No need to explain Kubernetes, Terraform or CI/CD pipelines
Evidence can include GitHub PRs, AWS CloudTrail logs or Jira tickets
Clear understanding of modern engineering practices
3. Helpful, not bureaucratic
Plain-English feedback
Collaborative approach
Practical recommendations that strengthen real security
4. Flexible delivery
Remote audits as standard
Asynchronous evidence review, where appropriate
Scheduling that works around your team
This approach ensures rigorous certification without unnecessary complications.
Request a clear, no-obligation quote today and see how quickly you can move towards ISO 27001 certification.
ISO 27001 certification requirements – FAQs
-
Yes. An organisation can align its ISMS with ISO 27001 requirements without undergoing certification. However, without an external audit, it cannot claim certified status. Many clients and public sector buyers require formal certification rather than self-declared compliance.
-
Yes. Controls implemented for SOC 2 or Cyber Essentials can often support ISO 27001. However, ISO 27001 requires a formal ISMS structure, risk methodology, internal audits and management reviews, which may not be fully covered by other frameworks.
-
The standard does not mandate a fixed frequency. Risk assessments must be reviewed at planned intervals, so an organisation will need to fix their own frequency of review (e.g. annual) with potential other reviews whenever significant changes occur, such as new systems, suppliers, or business models.
-
Yes. Outsourced services can be included within scope, but responsibility for information security remains with your organisation. Supplier controls, contractual requirements and monitoring must be evidenced.
-
Significant scope changes must be communicated to your certification body. Depending on the impact, a scope extension audit or reassessment may be required to maintain certification validity. Examples of this include: substantial growth in headcount, new products / services, new locations, new entities or companies within scope.
-
It is not legally mandatory. However, many UK or European public sector frameworks and enterprise contracts either require ISO 27001 certification or strongly prefer suppliers who hold it.
