SOC2 audit preparation:
A step-by-step guide
This guide explains SOC 2 audit preparation, covering scope definition, controls, evidence requirements, common pitfalls, and auditor expectations. It also provides a practical preparation framework and structured timelines to help organisations approach the SOC 2 audit with clarity and confidence.
Key takeaways
SOC 2 audit preparation is about real operational readiness, not only policies. Clear scope, defined control ownership, and consistent evidence matter more than documentation created only to satisfy the audit.
Strong evidence and timing determine audit success. Auditors test samples over a defined period, so controls must operate consistently, with accurate timestamps and traceable records collected well before audit fieldwork begins.
Structure and discipline reduce audit risk and delays. A clear preparation framework, realistic timeline, and role-based responsibilities help avoid common pitfalls, reduce exceptions, and result in a smoother, more predictable SOC 2 audit.
What is SOC 2 audit preparation?
SOC 2 is a recognised framework used to assess how a business protects customer data. It is based on standards set by the American Institute of Certified Public Accountants (AICPA).
Many UK and global clients now expect SOC 2 before they sign contracts, especially with SaaS (Software as a Service), cloud, and data-driven businesses.
In simple terms, SOC 2 shows that your systems, processes, and people handle data securely and consistently. It builds trust. It also reduces due-diligence questions from customers, partners, and investors.
SOC 2 audit preparation is everything you do before the formal audit begins.
It consists of internal readiness activities completed before you engage an accredited SOC 2 audit firm to carry out the independent audit. The goal is to make sure your organisation is genuinely audit-ready, not just “policy-ready”.
SOC 2 audit preparation focuses on:
Defining clear control ownership*
Implementing and documenting security and operational controls
Collecting reliable audit evidence
Ensuring controls* operate consistently in day-to-day work
This preparation stage is separate from the formal SOC 2 audit, which must be performed by an accredited auditor. Auditors can assess and report on controls, but they cannot design or fix them for you.
SOC 2 preparation applies to:
SOC 2 Type I - Evaluates the design of your controls at a specific point in time
SOC 2 Type 2 - Proving controls operate effectively over a defined period (usually 3-12 months)
Strong preparation reduces audit delays, limits remediation, and leads to a cleaner SOC 2 report.
Understanding controls and control ownership
*Controls - Controls are the policies, processes, and technical measures a business uses to protect data, manage risk, and ensure systems operate securely and consistently in day-to-day activities.
*Control ownership - Control ownership means clearly assigning responsibility for each control to a specific person or role, ensuring it is implemented correctly, maintained, and evidenced when required for audit.
How auditors assess SOC 2 readiness
SOC 2 auditors do not test everything. They assess whether your controls are well designed, consistently followed, and supported by evidence.
Here is how readiness is typically assessed.
1. Evidence sampling
Auditors review a representative sample of evidence, not every activity or transaction.
Samples must fairly represent normal operations across the audit period, not isolated examples or best-case scenarios.
2. Design vs operating effectiveness
For SOC 2 Type I, auditors assess whether controls are suitably designed at a specific point in time.
For SOC 2 Type II, they test whether those controls operated effectively over a defined period (typically 3 to 12 months).
3. Pre-fieldwork review
Before testing begins, auditors review:
System descriptions
Risk assessments
Control mappings against the Trust Services Criteria*
This helps confirm the audit scope and testing approach.
*Trust Services Criteria are the security, availability, confidentiality, processing integrity, and privacy principles used to assess how organisations protect and manage customer data.
4. Triggers for deeper testing
Auditors may expand testing if they find:
Missing or incomplete evidence
Control exceptions or inconsistencies
New or changed controls introduced mid-period
Unclear ownership or poorly defined processes
Strong preparation reduces follow-up questions and avoids extended testing.
Type I vs Type II: Audit prep differences
The preparation work for SOC 2 Type I and Type 2 is similar, but the evidence expectations are very different.
1. SOC 2 Type I preparation
Type I focuses on whether controls are designed correctly at a specific point in time.
Preparation centres on documented policies, defined processes, and clear control ownership.
2. SOC 2 Type 2 preparation
Type 2 requires evidence showing controls operated consistently over a defined period, typically three to twelve months. This includes logs, tickets, approvals, and monitoring records collected over time.
Type 2 is often premature if:
Controls were implemented recently
Controls have not been in place for at least three months
Processes are applied inconsistently across teams or systems
Auditors assess operating maturity by testing whether controls are repeatable, stable, and sustained, not one-off or manually enforced.
Strong preparation ensures evidence reflects real operational practice, not last-minute fixes.
Practical framework for SOC 2 audit preparation
This framework breaks SOC 2 audit preparation into clear, manageable steps. Each step builds audit readiness without adding unnecessary complexity.
Step 1 - Define scope & audit goals
Start by clearly defining what the SOC 2 audit will cover.
Identify:
In-scope systems, services, and environments.
Relevant Trust Services Criteria (Security is mandatory; others are optional).
Decide early whether you are preparing for SOC 2 Type 1 or Type 2, and confirm the audit period if Type 2 applies.
For many organisations, starting with Type 1 can make a later Type 2 smoother. A Type 1 audit clarifies how auditors interpret your scope, controls, and system description, which makes expectations clearer before committing to a longer operating period.
Just as important, document exclusions clearly. This prevents scope creep*, reduces audit effort, and avoids unexpected testing later.
*Scope creep means the audit gradually covers more systems, processes, or controls than originally agreed, increasing workload, cost, and audit risk without formal approval or planning.
Step 2 - Assign ownership & responsibilities
SOC 2 preparation fails without clear ownership.
Key roles should include:
Executive sponsor - Overall accountability and decision-making authority.
Security or compliance owner - Coordinates preparation and audit activity.
Control owners - Responsible for operating controls and providing evidence.
Avoid assigning responsibility without authority. Control owners must have the ability to enforce and maintain the controls they own.
Step 3 - Implement & validate controls
Each control must map clearly to the relevant Trust Services Criteria.
For every control, confirm it is:
Documented
Implemented in practice
Operating consistently across teams and systems
Early validation helps identify gaps before auditors do.
Step 4 - Collect evidence continuously
Evidence should be collected throughout the year, not rushed at audit time.
Typical SOC 2 audit evidence includes:
User access reviews
Incident response records
Change management tickets
Security awareness training logs
Organise evidence by control and date. Clear timestamps help auditors confirm operating effectiveness quickly.
Step 5 - Perform a readiness assessment
A readiness assessment acts as a mock audit.
It can be performed internally or by an independent third party. The review simulates auditor questions and testing approaches.
This step identifies:
Missing or weak controls
Incomplete or inconsistent evidence
Operational gaps that need remediation
Step 6 - Prepare audit documentation
Prepare a complete and consistent audit pack, including:
Policies and procedures
System descriptions
Control narratives
Evidence index
Management assertions
Clear documentation reduces follow-up questions and shortens audit timelines.
Step 7 - Management review & final prep
Before the audit starts, management should review readiness outcomes.
They should:
Approve remediation actions
Confirm audit scope and timeline
Ensure key staff availability during fieldwork
Strong management oversight signals maturity and improves audit outcomes.
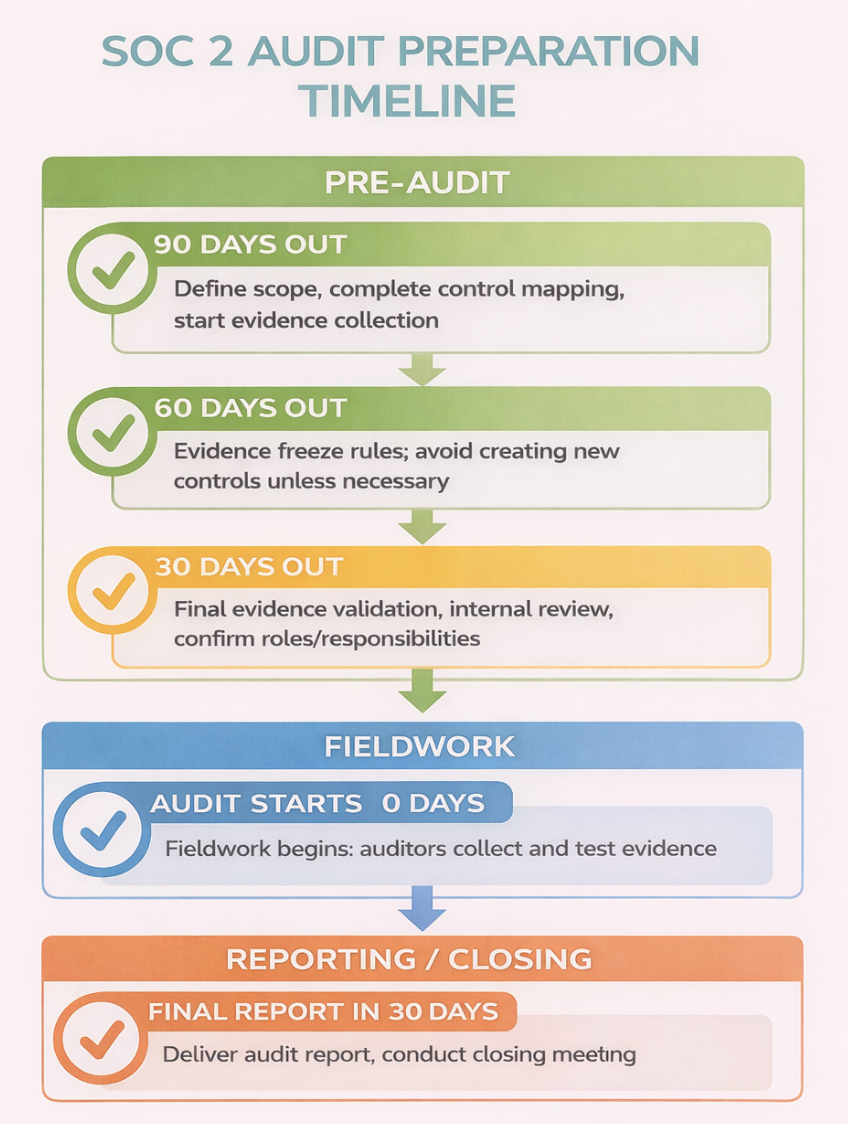
SOC 2 audit preparation timeline (with decision gates)
A clear timeline helps prevent last-minute gaps and reduces audit stress. Each stage acts as a decision gate before moving forward.
90 days before the audit
Define audit scope and objectives
Complete control mapping to the Trust Services Criteria
Begin structured evidence collection
60 days before the audit
Set evidence freeze rules
Avoid introducing new or changed controls unless critical
Focus on stabilising existing processes
30 days before the audit
Validate evidence completeness and quality
Perform final internal readiness review
Confirm roles, responsibilities, and auditor access
Run-up to the audit
Ensure all evidence is organised and clearly indexed
Provide evidence in the format requested by your auditor
Audit week
Do not change controls
Respond to auditor questions promptly
Maintain normal operations without last-minute fixes
Following these decision gates improves audit efficiency and reduces the risk of extended testing.
Evidence that passes vs evidence that fails
Auditors don’t just check whether evidence exists. They assess whether it clearly proves that controls are designed properly, used consistently, and supported by reliable records. Small gaps often lead to failed controls.
The following examples illustrate how auditors typically distinguish between acceptable and failed evidence.
Policies
Pass: Policies are complete, formally approved, dated, and actively followed by the business.
Fail: Policies are outdated, still in draft, missing approval records, or not reflected in real operations.
Access reviews
Pass: Access is reviewed on a defined schedule, with evidence showing who performed the review, what was checked, and what actions were taken.
Fail: Reviews are informal, irregular, undocumented, or lack clear ownership and outcomes.
Change management
Pass: Changes are logged, approved in advance, tested, and supported by rollback plans where required.
Fail: Changes are made without approval, documentation, or evidence of testing.
Logging and monitoring
Pass: Logs are complete, retained for the audit period, and clearly linked to security or operational controls.
Fail: Logs are incomplete, overwritten, missing timestamps, or cannot be traced back to specific controls.
Role-based SOC 2 preparation checklist
SOC 2 preparation works best when responsibilities are clearly split by role. Clear accountability reduces delays, improves coordination, and prevents evidence gaps during the audit. Each function should not only operate controls but also review and submit evidence when required.
CTO/Engineering
Implement and maintain technical security controls
Test controls and fix identified gaps
Collect and retain evidence for system access, changes, and infrastructure security
Review technical evidence before it is provided to the auditor
Security/IT
Perform and document regular access reviews
Maintain logging, monitoring, and alerting records
Produce reports showing ongoing control effectiveness
Validate the completeness of security evidence prior to submission
HR
Maintain HR policies and procedures
Keep security training records and attendance logs
Document background checks, onboarding, and offboarding activities
Review HR documentation to ensure it is current and audit-ready
Compliance Owner
Manage control mapping to the Trust Services Criteria
Coordinate evidence collection across teams
Track readiness status using a SOC 2 checklist
Review, organise, and formally provide evidence to the auditor
CEO/Leadership
Approve audit scope and objectives
Reinforce accountability across teams
Ensure time, budget, and resources are available for preparation and audit support
Review readiness status and confirm evidence is complete before fieldwork begins
Common SOC 2 audit pitfalls
Many SOC 2 audits run into trouble for practical, avoidable reasons. These issues often delay reports or trigger additional testing.
1. Missing historical evidence or inconsistent timestamps
Auditors rely on timestamps to confirm that controls operated during the defined audit period. When evidence is missing, undated, or inconsistent, auditors cannot verify timing, which weakens otherwise valid controls.
2. Controls implemented mid-period
When controls are introduced partway through the audit period, they cannot demonstrate consistent operation from start to finish. Without earlier evidence, auditors cannot assess full operating effectiveness, even if the control works well later.
3. Over-scoping the audit
Including systems or services that are not required by customers increases audit complexity. A broader scope means more controls, more evidence, and more testing, often without improving the value of the SOC 2 report.
4. Poorly written or incomplete system descriptions
System descriptions explain how data flows through your environment and where controls apply. If these are unclear or incomplete, auditors must ask follow-up questions and may expand testing to reduce uncertainty.
5. Insufficient or poorly organised evidence
Even strong controls can fail if evidence is difficult to review.
Large volumes of unstructured files slow the audit and increase the risk of missed or rejected evidence. Clear organisation and traceability are essential.
6. Controls not established before the Type 2 assessment window
This is often the most expensive mistake for first-time Type 2 audits, as it wastes internal effort and results in evidence that cannot be used due to timing issues.
As Rob Hall, Tempo Audits Founder, states:
"Ensuring that you have all the controls in place before the Type 2 assessment window starts is key. A Type 1 audit is a great way to solve this, but is more costly for companies. Failing that, they could also opt for some sort of readiness assessment before kicking off the assessment window. The risk if you don’t is that you can end up with an incorrect control structure in place, and get a report that Exceptions - which it’s best to avoid. Beyond that, making sure that the evidence is really well collected and gathered is helpful both for the client to check they’re readiness in advance, as well as for the auditor.”
Pre-audit readiness self-test
Before engaging your auditor, it is helpful to step back and assess whether your organisation is genuinely ready. This self-test highlights the areas auditors focus on most closely and where issues often arise.
Ask yourself the following questions:
Can you show evidence for all in-scope controls? Each control should be supported by clear, relevant documentation that demonstrates how it operates in practice, not just how it is intended to work.
Are timestamps accurate and traceable? Auditors rely on dates and time records to confirm when activities occurred and whether they fall within the audit period. Evidence without clear timestamps often leads to follow-up questions.
Are roles and responsibilities clearly documented? Auditors expect to see who owns each control and who is responsible for carrying it out. Clear ownership helps demonstrate accountability and consistency.
Have you validated control operation over the required period? For Type 2 audits, this means proving that controls operated reliably throughout the entire review window (3 to 12 months), not just at the end.
Finally, have you provided the auditor with the evidence in the format they requested? Well-organised, clearly indexed evidence in the correct format reduces review time and helps the audit progress smoothly.
If you can confidently answer yes to each of these points, you are well-positioned for a successful SOC 2 audit.
Knowing the post-audit reality
A SOC 2 audit does not always end with a perfect report, and that is normal. What matters is how findings are handled and how readiness is maintained afterwards.
1. Exceptions
If auditors identify areas where controls did not operate as expected, these are recorded as exceptions. Each exception documents the issue, its impact, and the steps taken or planned to address it.
2. Remediation letters
When deficiencies are corrected after the audit, remediation letters provide formal confirmation of the actions taken. These updates help demonstrate improvement to customers and stakeholders.
3. Bridge letters
If there is a gap between the audit period and when the report is issued or shared, a bridge letter may be used. This provides temporary assurance that controls have continued to operate since the audit period ended.
4. Ongoing readiness
SOC 2 is not a one-off exercise. Maintaining readiness requires continuous monitoring, regular evidence collection, and updating controls as systems and risks change.
Ongoing discipline makes future audits faster and less disruptive.
Ready to streamline your SOC 2 audit preparation?
Preparing for a SOC 2 audit can feel overwhelming, especially if it’s your first time going through the process.
One final tip - Request the evidence request list from your auditor as early as possible. Obtaining this early allows you to line up documentation, confirm ownership, and ensure everything is ready to be provided in the expected format before fieldwork begins.
We hope this article, with its key preparation steps, timeline, and essential checklists, is able to pave the path for a successful SOC 2 audit for your company.
Tempo Audits specialises in SOC 2 audits for modern tech and SaaS companies. We bring a remote-first, collaborative audit experience designed around how tech companies actually work, with clear communication and practical audit delivery that fits your timelines and workflow.
"Our approach is built on flexibility and agility. We are nimble enough to move to the time frames that a company needs, being really flexible about moving audit dates to fit your availability and readiness. Even within the audit, we work to the practices of a modern tech company. This means using the same tools as our clients, like Slack or Teams, to gather evidence and communicate, and ensuring our communication style and tone of voice match the way our customers work."
– Rob Hall, Tempo Audits Founder
Book a call with us to discuss your SOC 2 audit requirements, get a transparent quote, and plan your audit schedule.
Not sure if your business needs an ISO 27001 or SOC 2 audit? Read our expert guide.
FAQs
-
Readiness is internal prep, which can be delivered internally or by 3rd party consultants (who don’t need to be auditors); the formal audit produces the official SOC 2 report by an independent CPA.
-
Not necessarily. Internal teams can manage prep if they have sufficient knowledge, but often bring in consultants to support., Auditors can advise on mapping and evidence, as well as readiness.
-
Use timestamped documents/logs/screenshots linked to each control and indicate ownership.
-
Controls related to your chosen Trust Services Criteria. Your auditor can confirm exact requirements.
-
Missing evidence may trigger exceptions, remediation letters, or deeper auditor testing. Early prep avoids delays.
-
Yes, if clearly mapped and auditable.
-
Continuously, with formal review at least quarterly or after significant operational changes.
-
No, self-assessments identify gaps; only a licensed CPA can issue a valid SOC 2 report.
Also read:
