SOC 2 Type 1 Guide
This guide helps you understand SOC 2 Type 1 clearly, from what it is and when it makes sense, to preparation, costs, and common pitfalls. It explains how auditors assess readiness and how to plan confidently for SOC 2 Type 2.
Key takeaways
SOC 2 Type 1 provides fast, independent assurance that your security controls are correctly designed at a point in time, helping growing tech companies build trust, unblock sales, and start compliance confidently.
SOC 2 Type 1 is a starting point, not the end goal. It validates control design but not ongoing performance. Early planning is essential to avoid rework and ensure a smooth transition to SOC 2 Type 2.
Preparation and auditor guidance matter more than tools. Clear scope, ownership, documentation, and experienced auditor input reduce cost, avoid common exceptions, and set the foundation for long-term, scalable SOC 2 compliance.
What is SOC 2 Type 1?
SOC 2 Type 1 is an independent check that confirms whether a company has the right security and privacy controls in place at a specific point in time. Rather than testing how those controls operate over months, it focuses on whether the right safeguards are in place on the chosen assessment date.
The review looks at design suitability, not ongoing performance. In simple terms, it answers a basic but important question: have you designed controls that should work as intended? This makes SOC 2 Type 1 a useful first step for growing tech companies that need assurance quickly.
The assessment must be carried out by a SOC 2 audit firm - and the report must be issued by a AICPA-registered CPA firm in the US, or in the UK or Europe, a CIMA-registered accountancy firm. The outcome is a formal SOC 2 Type 1 report that provides a clear snapshot of control readiness.
Because it offers early assurance, SOC 2 Type 1 is often used to unblock near-term sales, satisfy customer due diligence, or prepare for a future SOC 2 Type 2 audit.
Understanding SOC 2
SOC 2 (System and Organisation Controls 2) is a widely recognised framework for evaluating how well a service organisation protects customer data against key criteria such as security, availability, processing integrity, confidentiality, and privacy.
SOC 2 reports are delivered by licensed CPAs or accounting firms, operating under professional bodies such as the AICPA (American Institute of Certified Public Accountants - primarily in the US) or CIMA-regulated firms (Chartered Institute of Management Accountants) in Europe and other regions. This makes SOC 2 a trusted assurance framework for cloud and technology businesses worldwide.
The importance of SOC 2 compliance
As data security becomes a deciding factor in buying decisions, customers want more than promises. They want clear evidence that a business understands its risks and has taken practical steps to manage them.
This is where SOC 2 compliance plays an important role, especially for growing tech companies working with sensitive customer data.
1. Protects customer data and reduces risk
SOC 2 compliance demonstrates that your organisation has defined controls to protect customer data. It shows that security risks are identified, managed, and not handled in an ad-hoc way.
2. Builds trust and signals security maturity
For customers, SOC 2 acts as a trust signal. It reassures them that your business takes security seriously and has reached a recognised level of operational maturity.
3. Supports enterprise sales and procurement
SOC 2 is often required when selling to larger or enterprise customers. Having it in place helps reduce sales friction by addressing security concerns early and preventing deals from stalling.
4. Creates a foundation for long-term compliance
By documenting and maintaining controls, SOC 2 helps establish a structured approach to risk management. This makes future audits, including SOC 2 Type 2, easier to manage.
5. An attestation, not a certification
SOC 2 compliance is an independent attestation, not a certificate. An auditor assesses whether your controls meet the required criteria rather than issuing a simple pass or fail result.
6. Especially important for establishing trust in the US
SOC 2 is the prevailing security standard in the US. If your current or target customers are US-based (even if you’re based in US), SOC 2 is often expected, whereas ISO 27001 is more commonly requested in Europe.
Related read: ISO 27001 vs. SOC 2: Which certification is right for your business?
SOC 2 Type 1 vs Type 2: Audit Reality
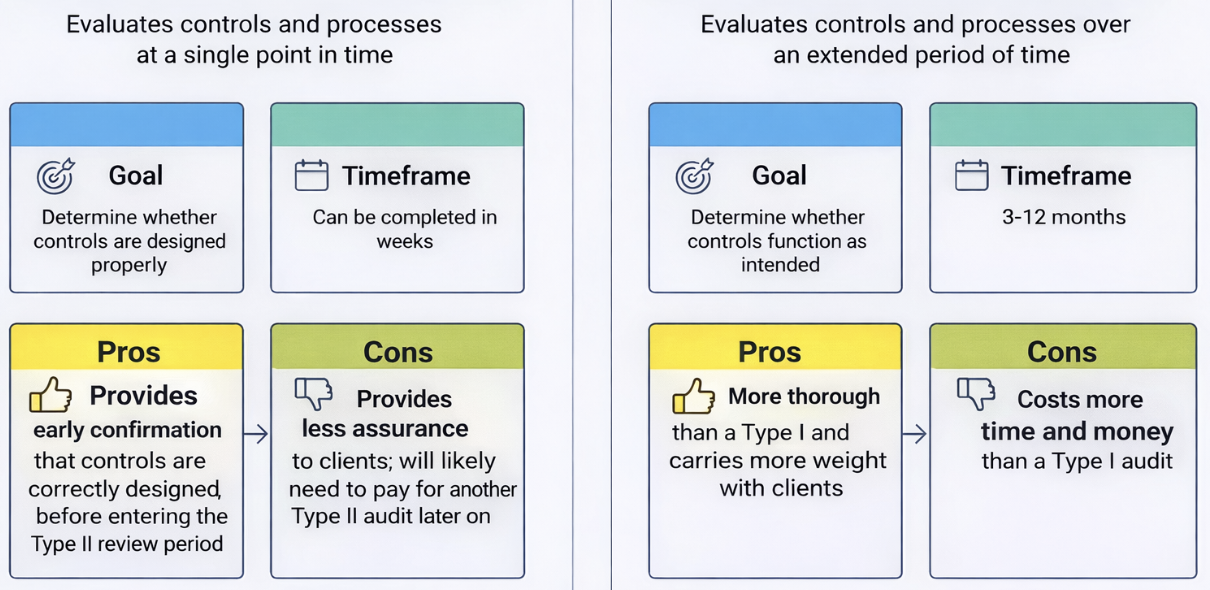
SOC 2 Type 1 and Type 2 serve different purposes, and understanding the practical difference is important when planning your compliance journey.
SOC 2 Type 1 evaluates whether your controls are designed suitably at a single point in time. It confirms that the right policies, processes, and safeguards exist on the assessment date. However, it does not show whether those controls are followed consistently or work in practice over time.
SOC 2 Type 2, on the other hand, evaluates both control design and operational effectiveness over a defined period, typically three to twelve months. This means auditors test evidence to confirm that controls are not only well designed but are actually operating as intended on an ongoing basis.
Because of this, SOC 2 Type 1 does not demonstrate long-term consistency or sustainability. It is often seen as an entry point, while SOC 2 Type 2 is usually required by more mature enterprise buyers who want assurance that controls are embedded into day-to-day operations.
SOC 2 Type 1 should be planned carefully because its purpose is to support a smooth transition to SOC 2 Type 2. When controls are thoughtfully designed and properly scoped during Type 1, organisations reduce the risk of delays, rework, or complications during the longer Type 2 audit period.
We’ve summarised the comparison in the illustration below:
When SOC 2 Type 1 makes sense
SOC 2 Type 1 is a good fit when:
Your security and privacy controls have been recently implemented and need independent validation.
You need quick assurance to support an active deal, partnership, or customer review.
Your organisation is early in its compliance journey and wants a clear starting point.
There has been a significant scope change (for example, a new company acquisition or a new cloud service offering), and you need updated assurance.
You intend to progress to SOC 2 Type 2, and want to make sure your controls are designed correctly before starting the monitoring period
A client wants confirmation that your controls are set up properly before committing to or reviewing your SOC 2 Type 2 audit.
SOC 2 Type 1 audit preparation made easy!
At Tempo Audits, we know a SOC 2 audit can be daunting, so we have curated a list of FAQs to help you prepare for both SOC 2 Type 1 and SOC 2 Type 2 audits. For any questions, you can also easily reach out to us at hello@tempoaudits.com.
When SOC 2 Type 1 is the wrong choice
SOC 2 Type 1 may not be the right option in the following situations:
Systems or infrastructure are complex or changing frequently, which can make a point-in-time review less meaningful.
A SOC 2 Type 2 audit is planned very soon, and the organisation is already confident that controls are correctly designed.
The organisation wants to conserve budget and is comfortable progressing directly to SOC 2 Type 2.
A SOC 2 Type 1 audit has already been conducted, and there is no material change in scope that would justify repeating it.
What is included in a SOC 2 Type 1 report?
A SOC 2 Type 1 report provides a clear, structured view of how your controls are designed at a specific point in time. It is written for customers, prospects, and stakeholders who need assurance - not technical detail.
A typical SOC 2 Type 1 report includes:
Auditor’s opinion - A formal statement confirming whether controls are suitably designed as of the assessment date.
Management’s system description - An overview of your services, systems, boundaries, and how controls are intended to operate.
Defined scope and Trust Services Criteria - A clear explanation of what is in scope and which criteria are covered (security, availability, processing integrity, confidentiality, privacy).
Control descriptions - Detailed explanations of each control, including purpose and ownership.
Exceptions, if any - Noted gaps or design issues, along with context for remediation where applicable.
This report acts as a concise snapshot of control readiness and is often shared during security reviews and procurement processes.
3 steps towards a SOC 2 Type 1 attestation
Achieving SOC 2 Type 1 follows a clear and structured process. The goal is to confirm that your controls are designed correctly, not to prove how they perform over time.
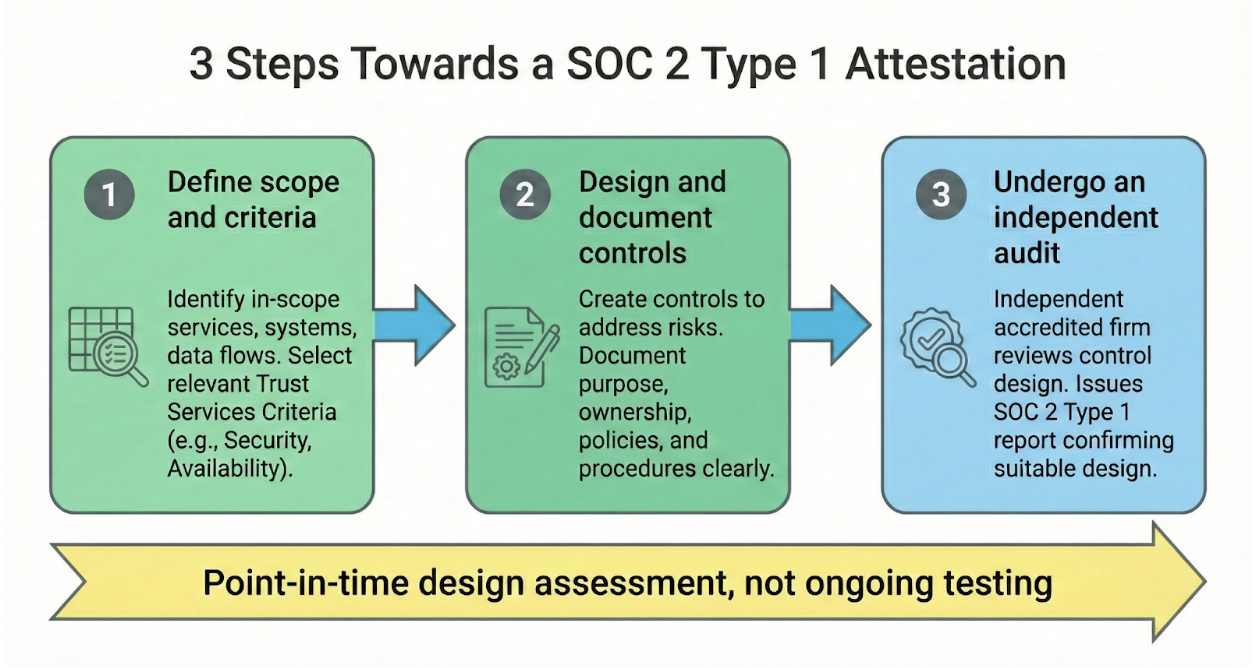
1. Define scope and criteria
Start by identifying what is included in the audit.
This means defining the in-scope services, systems, and data flows, and selecting the relevant Trust Services Criteria (such as Security, Availability, or Confidentiality).
A well-defined scope keeps the audit focused and avoids unnecessary complexity.
2. Design and document controls
Next, design controls that address identified risks and document them clearly.
Each control should have a clear purpose, defined ownership, and supporting policies or procedures. This step ensures auditors can understand how risks are meant to be managed.
3. Undergo an independent audit
An independent, accredited SOC 2 audit firm reviews the control design and issues the SOC 2 Type 1 report. This confirms whether controls are suitably designed as of the assessment date.
Quick SOC 2 Type 1 audit checklist
Use this checklist to confirm you are ready for a SOC 2 Type 1 audit and to avoid common delays or exceptions.
Clear understanding of what is in and out of scope
In-scope systems, services, and data flows identified
Relevant Trust Services Criteria selected
Controls designed to address identified risks
Each control has a named owner
Policies reflect how the business actually operates
Controls are clearly documented and easy to understand
Evidence prepared and organised as requested by the auditor
Internal readiness review completed
Stakeholders aligned on audit timelines and expectations
This checklist helps ensure your SOC 2 Type 1 audit stays focused, efficient, and aligned.
How auditors assess SOC 2 Type 1 readiness
1. Reviewing control design and risk alignment
Auditors first assess whether controls are designed to address real and relevant risks. They look for a clear link between identified risks and the controls intended to manage them.
2. Confirming controls are implemented as described
Auditors review evidence to confirm that controls exist in practice, not just on paper.
This includes checking policies, procedures, and system settings to ensure they match the documented control descriptions.
3. Checking consistency across documentation and systems
Consistency is crucial. Auditors compare policies, procedures, and system configurations to confirm they align with each other and reflect how the organisation actually operates.
4. Applying professional judgement where clarity is lacking
If controls are vague or poorly defined, auditors apply professional judgement.
Unclear wording or missing details often lead to follow-up questions or required updates.
5. Identifying early red flags
Auditors also look for early warning signs, such as unclear scope, missing control owners, or incomplete documentation.
Addressing these issues early helps avoid delays and keeps the audit process smooth.
6 auditor-approved tips to prepare for a SOC 2 Type 1 audit
1. Clarify what the auditor will review
Before the audit begins, make sure there is a shared understanding of which systems, services, and data the auditor will assess. Clear expectations at this stage help prevent scope changes and delays later on.
2. Assign a clear owner to every control
Make sure each control has a named owner who understands how it works and can answer auditor questions. This avoids confusion and speeds up responses during audit fieldwork.
3. Make sure policies match day-to-day operations
Review your policies and confirm they reflect how your organisation actually operates. Auditors will look for consistency between written documents and real practices.
4. Link each control to the Trust Services Criteria
Clearly map every control to the relevant Trust Services Criteria (Security, Availability, Processing Integrity, Confidentiality, Privacy).
This helps auditors understand why a control exists and which risk it is designed to address.
6. Run a readiness check before audit fieldwork
Carry out an internal review to identify gaps, unclear wording, or missing evidence. Addressing these issues early reduces audit pressure and last-minute fixes.
6. Organise evidence in advance
Gather evidence ahead of time and present it in the format requested by your audit firm. Well-organised evidence reduces back-and-forth and helps the audit progress smoothly.
Common SOC 2 Type 1 exceptions
During a SOC 2 Type 1 audit, certain issues appear more frequently than others. These exceptions usually relate to clarity, ownership, and alignment rather than technical gaps.
Policies that do not align with controls - Written policies describe one approach, but the actual controls in place follow a different process.
Controls without clear ownership - Controls exist, but no one is clearly responsible for maintaining or explaining them.
Over-scoped environments - Too many systems or services are included, increasing audit exposure and complexity without adding value.
Inconsistent or incomplete documentation - Evidence is missing, outdated, or inconsistent across policies, procedures, and systems.
Planning a SOC 2 Type 1 audit?
Tempo Audits is here to help! Our auditors have extensive experience conducting internal and external audits. They can assist you with your questions. Meet our auditors here.
For quick assistance, drop us an email at hello@tempoaudits.com.
SOC 2 Type 1 attestation: How much does it cost?
The cost of a SOC 2 Type 1 attestation depends largely on how complex your organisation is and how well prepared you are before the audit begins. There is no fixed price, as auditors assess the level of effort required based on scope, systems, and documentation quality.
In most cases, audit fees typically range from £4,000 to £16,000 or more. The lower end usually applies to smaller, well-prepared organisations with a narrow scope, while higher costs are associated with broader or more complex environments.
Costs tend to increase when:
The organisation is larger or more operationally complex
Multiple systems and platforms are included in scope
Several Trust Services Criteria are selected
Documentation is incomplete or inconsistent
In addition to audit fees, some organisations incur additional costs. These may include readiness support, internal remediation work, or help addressing gaps identified before the audit.
It is also worth noting that lower costs usually come from better preparation, not fewer controls. Clear scope definition, strong documentation, and organised evidence reduce audit effort and help keep fees under control.
Post-audit reality (What happens after)
Once the SOC 2 Type 1 review is completed, the auditor issues the final report. This confirms whether your controls were suitably designed as of the assessment date and marks the formal close of the audit.
If the auditor identifies any issues, these are recorded as exceptions. Exceptions highlight gaps in control design or documentation and are typically accompanied by clear remediation actions. These do not automatically invalidate the report, but they do require attention and structured follow-up.
After remediation, organisations are often expected to retain supporting evidence showing that corrective actions were completed. This may include:
Updated policies or procedures
Revised control descriptions
Screenshots or system configuration updates
Meeting minutes confirming ownership changes
Logs or records demonstrating corrected implementation
In some cases, organisations issue remediation letters. These formal updates explain what was fixed after the audit date and may reference the supporting evidence retained internally.
Bridge letters may also be used between audit periods. These confirm that controls have not materially changed since the last report and that no significant incidents have affected the control environment.
Finally, maintaining readiness is essential. SOC 2 Type 1 should be treated as a stepping stone, with controls applied consistently and evidence retained regularly to support a smooth transition into SOC 2 Type 2, where ongoing operation will be formally tested over time.
Why an auditor-led approach matters
An auditor-led approach provides clarity and judgment that tools alone cannot offer. Experienced auditors look beyond checklists to understand whether controls truly make sense for your organisation and the risks you face.
Auditors assess:
Control intent - Why a control exists and what risk it addresses.
Design logic - Whether the control is practical and appropriate.
Risk coverage - Whether key risks are adequately managed.
Having an impartial third-party auditor is also intrinsic to SOC 2. The attestation must be carried out by an accredited firm in the UK and Europe, which gives the report credibility and trust.
It is important to recognise that templates and automation tools have limits, as:
They do not replace professional judgment
They cannot validate whether the control design is defensible
They often fail to account for business-specific risks
Working closely with an auditor helps:
Reduce rework
Avoid misaligned expectations
Create a smoother, more predictable audit journey
This approach is especially valuable for fast-moving tech companies planning to scale their compliance programme.
How Tempo Audits approaches SOC 2 Type 1 differently
Tempo Audits takes a practical, auditor-led approach that is designed for modern tech companies and scaling startups, not generic compliance exercises.
The core of our approach is to make the audit feel built for the client. We understand that our clients, particularly founders and early-stage teams, wear multiple hats and are not dedicated information security professionals.
That's why the experience is fast-moving, agile, and collaborative. We leverage tools like Slack or Teams for communication and aim to keep contact time to a minimum, allowing your team to get on with their busy workloads.
Our communication is always clear and supportive to ensure a smooth process that respects your time.
Here’s why our approach stands out.
Client-first mindset - Engagements are led by experienced auditors who apply professional judgment, not just checklists, and aim to be helpful. This ensures controls are sensible, defensible, and aligned to real risks - especially for start-ups building structured processes for the first time.
Tech-stack-aware audits - Audits are conducted with an understanding of modern cloud platforms and SaaS environments. Also, controls are assessed in the context of how your systems actually work.
Plain-English communication - Explanations are clear and jargon-free, making it easier for founders, engineers, and operations teams to stay aligned throughout the audit.
Remote-first execution - The process is built to work remotely, reducing disruption and fitting naturally into distributed team workflows across the UK and Europe.
Designed for SOC 2 Type 2 success - Decisions made during Type 1 are structured to support a smooth transition to Type II, reducing rework, delays, and future audit friction.
If you wish to speak to our team to discuss your SOC 2 audit requirements, we are just a call away.
FAQs (Auditor Answers)
-
Yes - especially for fast-moving startups. It demonstrates that controls are in place, giving prospects confidence while you continue building toward Type 2.
-
Yes. If your team wants to progress straight for Type 2, you can - but Type 1 gives assurance that your controls are correctly in-place ahead of the Type 2. It is also faster, cheaper, and often helps secure early deals.
-
Typically 4–12 weeks for Type 1, depending on scope, team readiness, and existing controls.
-
Incomplete documentation, untested or poorly defined controls, and missing evidence for key Trust Services Criteria.
-
As a snapshot: they show controls are designed correctly at a point in time, signaling commitment to security, but not yet proving long-term operational effectiveness.
-
Type 1 readiness verifies control design at a moment in time, while ongoing compliance ensures controls are consistently applied, monitored, and improved between audits.
-
No, the preparation does not require an auditor - it can be delivered internally (if you have the competence) or through 3rd party consultants. Internal readiness reviews help, but an independent CPA attestation is required to issue the official SOC 2 Type 1 report, rather than the preparation.
-
Controls should be clear enough that any auditor can understand intent, ownership, and operation - practical, not just theoretical. Examples, logs, and policies improve defensibility.
-
Yes. A Type 1 audit highlights weaknesses early, allowing teams to remediate issues and strengthen operational processes before the longer Type 2 review.
-
By centralising evidence, assigning clear control owners, and maintaining consistent virtual processes, distributed teams can prepare and respond efficiently without delaying the audit.
