SOC 2 Type 2 compliance: A complete guide [2026]
This guide explains what SOC 2 Type 2 compliance really involves and why it matters for growing organisations. It walks through the audit process, costs, timelines, and practical considerations, helping businesses understand how to prepare, succeed, and maintain long-term assurance with confidence.
Key takeaways
SOC 2 Type 2 proves long-term security. It shows that controls are not only well designed but consistently followed over time, giving enterprise customers stronger confidence than a point-in-time assessment.
Preparation, ownership, and evidence discipline determine success. Clear scoping, named control owners, continuous evidence collection, and internal reviews reduce audit risk, lower costs, and make annual SOC 2 Type 2 renewals far smoother.
SOC 2 Type 2 is a commercial enabler, not only a compliance exercise. For UK and European companies selling globally (and particularly into the US), it supports enterprise deals, meets cross-border data expectations, and aligns security assurance with real customer and regulatory demands.
What is SOC 2 Type 2?
SOC 2 Type 2 is an independent audit that examines how well an organisation protects customer data over time. It does not only look at whether controls exist on paper; it also checks whether those controls work effectively in day-to-day operations.
Unlike the one-time assessment of a SOC 2 Type 1, a SOC 2 Type 2 audit covers a defined observation period. This is usually between 3 and 12 months. During this time, auditors test real evidence to confirm that security and data protection practices are consistently followed.
The audit is measured against the Trust Services Criteria. These include security, availability, processing integrity, confidentiality, and privacy. Each criterion focuses on a different aspect of how systems and data are managed.
The final SOC 2 Type 2 report is formally signed off by a licensed CPA firm. This makes it a trusted assurance document for customers, partners, and regulators.
What is SOC 2?
SOC 2 (System and Organisation Controls 2) is an independent compliance report based on standards developed by the American Institute of Certified Public Accountants (AICPA). The report is issued by licensed auditors operating under recognised professional bodies, including AICPA-accredited firms (primarily in the US) and CIMA-regulated firms (Chartered Institute of Management Accountants) in Europe and other regions.
SOC 2 evaluates a service organisation’s controls against the Trust Services Criteria - Security, Availability, Processing Integrity, Confidentiality, and Privacy - to demonstrate how customer data is protected and managed.
Note: Although commonly referred to as ‘certification’, SOC 2 Type 2 is technically an attestation report issued by an independent auditor.
SOC 2 Type 2 vs Type 1
SOC 2 Type 1 and SOC 2 Type 2 both assess how an organisation manages and protects customer data. The key difference lies in timing and depth.
A SOC 2 Type 1 audit looks at whether your controls are designed correctly at a specific point in time. It answers a simple question: Are the right controls in place today? Because it does not assess ongoing performance, Type 1 is often faster to complete.
SOC 2 Type 2 goes further. It examines whether those controls operate effectively over time, usually across a period of 3 to 12 months. This makes Type 2 more demanding, but also more valuable to customers, partners, and regulators.
Many organisations use SOC 2 Type 1 strategically. It can help unblock commercial deals, demonstrate early commitment to security, and act as a structured step toward a full SOC 2 Type 2 audit framework.
The table below summarises the practical differences buyers and auditors care about most.
SOC 2 Type 1 vs SOC 2 Type 2: Comparison table
| Area | SOC 2 Type 1 | SOC 2 Type 2 |
|---|---|---|
| Audit Focus | Design of controls | Design and operating effectiveness |
| Time Coverage | Point in time | Defined period (3-12 months) |
| Evidence Required | Policies and control design | Ongoing operational evidence |
| Audit Complexity | Lower | Higher |
| Audit Cost | Lower | Higher |
| Typical Use | Deal enablement, readiness | Customer assurance and compliance |
| Long-term Assurance | Limited | Strong and repeatable |
Speaking of comparison, many organisations wonder if they require a SOC 2 audit or an ISO 27001 audit. Here’s our guide on ISO 27001 vs. SOC 2 to make the decision easy for you.
What a SOC 2 Type 2 report covers and includes
A SOC 2 Type 2 report provides a detailed view of how an organisation manages and protects customer data over an extended period.
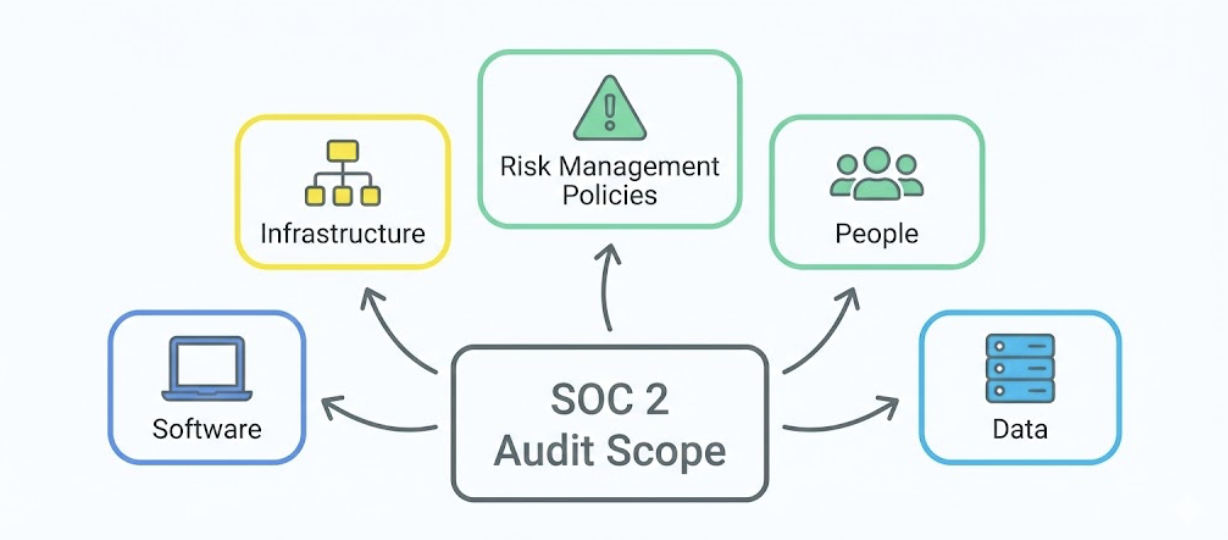
At a high level, the report covers control design and operational effectiveness across the agreed audit period, typically between 3 and 12 months. This includes controls related to infrastructure, software, data handling, risk management policies, and the people responsible for operating those controls. Each area is reviewed to ensure controls are not only defined but consistently followed in real-world operations.
The report itself is comprehensive. It includes clear descriptions of each control, the testing performed by the auditor, the evidence reviewed, and the results of that testing. Any exceptions or gaps are also documented, alongside the auditor’s formal opinion.
For UK and European organisations, the report carries additional weight in enterprise contracts. Buyers often expect alignment with GDPR obligations and recognised audit standards, as well as assurance from a reputable audit firm.
A typical SOC 2 Type 2 report contains four core sections:
The Auditor’s Report, which provides the independent opinion.
The Management Assertion, confirming responsibility for controls.
The System Description, explaining how systems and processes operate.
The Description of Trust Services Criteria and Controls, including test procedures and results.
Get a SOC 2 Type 2 report from experienced, accredited auditors!
If a SOC 2 Type 2 report is on your mind, worry not - our expert auditors are here to make it easy for you. We are a remote-first, tech-savvy firm with highly experienced auditors specialising in conducting SOC 2 audits and preparing organisations for necessary certification. Get in touch with us at hello@tempoaudits.com today.
Benefits of SOC 2 Type 2 compliance
Builds enterprise trust and reduces vendor friction - A SOC 2 Type 2 report gives buyers independent assurance, helping security reviews move faster and reducing repeated due-diligence requests.
Reduces data breach and regulatory risk - Ongoing testing of controls helps identify weaknesses early. This lowers the risk of security incidents and compliance failures.
Strengthens internal security culture and readiness - Clear ownership of controls improves accountability, embeds security into daily operations, and prepares teams for audits and customer reviews.
Supports US enterprise procurement requirements - SOC 2 Type 2 is often expected by US customers. Being compliant makes it easier to qualify for tenders and close enterprise deals.
Meets UK and European cross-border trust expectations - The report helps reassure clients and partners that data is protected in line with international standards, supporting GDPR-aligned and global data processing arrangements.
Who needs a SOC 2 Type 2 report?
SaaS, cloud, and technology providers serving enterprise clients - Organisations that host, process, or manage customer data are often required to provide SOC 2 Type 2 reports during vendor risk and procurement reviews.
Companies targeting the US or global markets - SOC 2 Type 2 is widely expected by US-based customers and multinational organisations, making it essential for businesses selling internationally.
Startups, mid-market, and enterprise vendors demonstrating security maturity - Businesses at any growth stage use SOC 2 Type 2 to show that their security controls are established, consistently applied, and ready for enterprise-level scrutiny.
Cost and time estimates
SOC 2 Type 2 costs and timelines vary based on company size, system complexity, and how prepared the organisation is before the audit begins.
Small to mid-sized organisations
Typical audit costs range from £10,000 to £20,000 (approximately €11,000 to €22,000). These audits usually cover a narrower scope with fewer systems and controls.
Large or complex enterprise environments
Costs often start at £30,000 and can exceed £100,000 (around €35,000 to €110,000+), depending on the number of systems, locations, and Trust Services Criteria in scope.
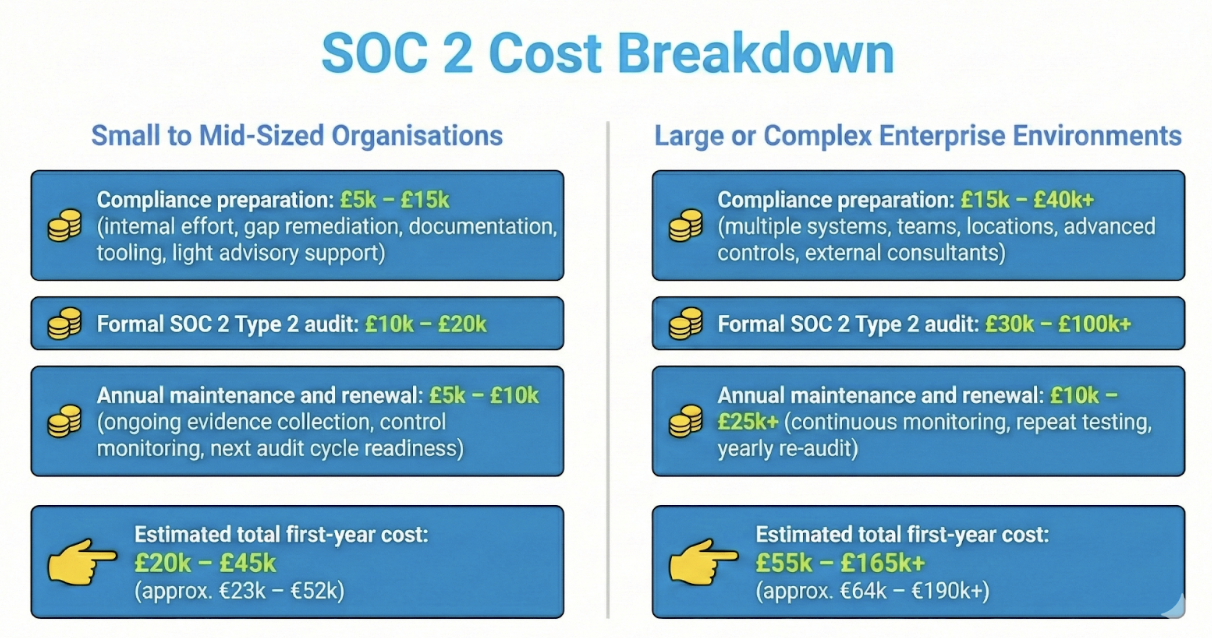
The first year is always the most expensive, although not necessarily. In later years, costs may reduce as controls mature and evidence collection becomes routine.
Preparation time
Preparation typically takes 4 to 26 weeks. The timeline depends on the size of the organisation, audit scope, maturity of existing controls, and how complete policies and evidence are at the start.
For small to mid-sized organisations, preparation typically takes 4 to 12 weeks. This usually includes defining scope, documenting controls, closing minor gaps, and collecting initial evidence where security processes are already in place.
For large or complex enterprises, preparation can take 12 to 26 weeks. Larger organisations often need more time to align multiple teams, standardise controls across systems, address gaps, and complete documentation and evidence collection.
SOC 2 Type 2 audit checklist
Below is a practical checklist that reflects how SOC 2 Type 2 audits typically run in real-world environments, from preparation through to ongoing compliance.
1. Pre-audit
☐ Define scope and map controls to the Trust Services Criteria
Clearly identify which systems, processes, and data are in scope, and map existing controls to the relevant Trust Services Criteria.
☐ Conduct a risk assessment and readiness review
Assess current control maturity (consistency and effectiveness of controls) to identify gaps early and reduce audit risk during testing.
☐ Assign control owners and consolidate evidence
Allocate responsibility for each control and gather policies, logs, approvals, and operational records in a structured way.
☐ Prepare evidence in the auditor’s preferred format
Ensure evidence is organised and accessible in the format required by auditors, often using a dedicated compliance platform.
2. Audit execution
☐ Provide the system description
Management prepares and submits a detailed system description. This explains the services in scope, infrastructure, software, data flows, control environment, and the boundaries of the audit. The auditor reviews this carefully, as it forms the foundation of the SOC 2 Type 2 report.
☐ Define the evidence request list
The auditor issues a structured evidence request list based on the agreed scope and Trust Services Criteria. This list outlines exactly what documentation, logs, reports, and records are required for testing.
☐ Provide and exchange evidence
The organisation uploads and shares evidence in line with the request list. This often includes access reviews, change management records, incident logs, policy documents, and monitoring reports. Evidence is typically exchanged through secure audit or GRC platforms to maintain efficiency and traceability.
☐ Handle follow-ups and clarifications
Auditors review submitted evidence and may raise follow-up questions or request additional samples. Timely responses and clear communication are essential to keep the audit on schedule and avoid delays.
☐ Audit window
At Tempo Audits, the audit is conducted within a two-week audit window, helping minimise disruption. This is enabled by leveraging platforms like Pillar (through our partner, Sensiba) and by working with customers who use dedicated GRC platforms like Vanta and Drata, allowing for highly efficient evidence collection and review.
3. Post-audit
☐ Remediation letters for any exceptions
Identified control gaps are documented, with clear ownership and remediation timelines.
☐ Bridge letters if interim assurance is required
These may be used to provide assurance between audit periods for customers or stakeholders.
☐ Continuous monitoring and improvement
Controls are refined and monitored throughout the year to prepare for the next audit cycle, which typically runs on a 12-month basis.
How long is a SOC 2 Type 2 report valid?
A SOC 2 Type 2 report does not “expire” in a technical sense. However, it reports on a specific audit period that has already elapsed, typically covering 3 to 12 months in the past. The assurance provided applies only to that defined period.
Because the report is backwards-looking, enterprise clients and procurement teams usually expect a recent and relevant report, often one issued within the last 12 months. If the covered period becomes too old, customers may request updated assurance.
For this reason, most organisations treat SOC 2 Type 2 as an annual cycle rather than a one-off project. Ongoing planning, continuous evidence collection, and control monitoring ensure readiness for the next reporting period and help maintain uninterrupted customer confidence.
What every organisation needs to know about SOC 2 Type 2 reports
Type 1 and Type 2 serve different strategic purposes - SOC 2 Type 1 provides a one-off snapshot of control design at a specific point in time. It is often used as a stepping stone to SOC 2 Type II to help organisations demonstrate progress, unblock deals, and prepare for long-term assurance.
SOC 2 Type 2 requires continuous ownership and evidence - Unlike Type 1, SOC 2 Type 2 depends on controls operating effectively over time. Continuous evidence collection and clear internal ownership are essential to avoid audit delays and repeated remediation.
UK and Europe-specific audit considerations matter - Organisations should account for local auditor expectations, GDPR alignment, and cross-border data handling (managing data across international jurisdictions). These factors are especially important when supporting enterprise contracts and international customer assurance requirements.
4 practical tips for SaaS and tech companies
Tip 1 - Use SOC 2 Type 1 as a foundation for Type 2 readiness
Treat SOC 2 Type 1 as a structured rehearsal rather than a standalone goal.
Use the findings to refine control design, confirm audit scope, and identify gaps early. Addressing these issues before the observation period begins makes the SOC 2 Type 2 audit more predictable and less disruptive.
Tip 2 - Prioritise human-led evidence reviews before relying on automation
Automated compliance tools can streamline evidence collection, but they cannot always assess context or quality.
Assign experienced team members to review evidence for completeness, relevance, and accuracy before submission. This reduces back-and-forth with auditors and prevents avoidable exceptions.
Tip 3 - Assign clear control ownership and rehearse internally
Every control should have a named owner who understands how it operates and what evidence is required. Running internal audit rehearsals helps teams practise responding to audit questions, validate evidence trails, and uncover gaps before formal testing begins.
Tip 4 - Implement structured, centralised evidence management
Maintain a single, well-organised repository for policies, logs, approvals, and audit artefacts. Use consistent naming, access controls, and version tracking.
This improves audit efficiency, supports ongoing monitoring, and reduces preparation effort in future audit cycles.
Common pitfalls and auditor insights
Over-scoped audits or unclear control ownership - Many organisations include too many systems or processes in scope without assigning clear ownership. This increases audit effort, creates gaps in evidence, and often leads to avoidable findings. Tight scoping and named control owners reduce complexity and risk.
Incomplete, inconsistent, or misaligned documentation - Auditors frequently see policies and records that are outdated, incomplete, or inconsistent across teams. Documentation should accurately reflect how controls operate in practice and be reviewed regularly to remain audit-ready.
Misalignment between policies and day-to-day operations - Well-written policies alone are not enough. Auditors test whether controls are actually followed in daily workflows. Any mismatch between written procedures and real behaviour is likely to result in exceptions.
Moving directly to Type 2 without validating controls - Organisations that skip a SOC 2 Type 1 or formal readiness assessment often implement controls incorrectly. A Type 1 audit or readiness review helps validate control design and implementation before the Type 2 observation period begins, reducing the risk of costly remediation.
Become SOC 2 compliant with an accredited firm!
Build trust with customers and meet enterprise security expectations with confidence. Tempo Audits supports you with SOC 2 compliance, with clear guidance and accredited audit expertise tailored to your business. Request a free quote today.
SOC 2 Type 2 - FAQs
-
The minimum audit period is 3 months, which is commonly used for an initial SOC 2 Type 2 assessment. After this first cycle, organisations usually move to a 12-month audit period, as this is what most enterprise customers expect.
-
Yes. SOC 2 Type 2 can include multiple systems or services, as long as each one is clearly defined in scope.
You must also provide evidence showing that controls operate effectively across all included systems, not just a subset.
-
The core audit process is largely the same. However, UK and European auditors may request additional context around local regulations, GDPR obligations, cross-border data handling, and client contractual requirements.
In most cases, these requests depend more on where your customers are located than where your business is based.
-
Internal audits are not mandatory for SOC 2. That said, they are highly beneficial for readiness.
Smaller organisations often find that one internal audit per year before the external audit is sufficient. Larger or more complex organisations may benefit from quarterly internal reviews to ensure controls remain consistent and gaps are addressed early.
-
No. Automation is not required. Tools can improve efficiency and help collect evidence, but human review remains crucial. Teams still need to confirm that evidence is accurate, complete, and truly reflects how controls operate in practice.
-
No. A bridge letter can only provide temporary assurance when there is a gap between audit periods. It does not replace a SOC 2 Type 2 report and is not accepted as a long-term substitute by enterprise clients.
-
Common issues include insufficient evidence, unclear control ownership, inconsistent or outdated policies, limited staff awareness, and poor documentation practices. These challenges often cause delays even when technical controls are strong.
-
No. SOC 2 Type 2 provides assurance that controls are designed well and operate effectively over time. It reduces risk, but it does not eliminate all security threats or guarantee that incidents will never occur.
-
Sometimes. Many controls overlap, such as access management, logging, and incident response. Typically, there is around 60–70% control overlap. However, evidence still needs to be mapped to SOC 2’s Trust Services Criteria and may require additional context.
-
Organisations should clearly document data flows (movement of data between systems), hosting locations, access controls, and applicable regulatory safeguards (controls meeting legal compliance requirements).
This helps satisfy auditor expectations and provides reassurance to enterprise clients handling international data.
