ISO 27001 controls explained
Annex A & the 93 controls (2026 guide)
This guide explains ISO 27001 controls, Annex A structure, audit expectations, common failures, and how to implement controls correctly.
Key takeaways
ISO 27001 controls are practical safeguards chosen to reduce your real risks, not a checklist you must complete in full.
The 93 Annex A controls (taken from the controls in ISO 27002) cover organisational, people, physical, and technological areas, but auditors assess effectiveness, not simply control adoption.
Passing the audit depends on clear ownership, regular reviews, and strong evidence showing your controls operate consistently over time.
ISO 27001 controls are the safeguards and measures an organisation uses to protect its information. They are not a one-size-fits-all checklist - you only implement the ones that address your risks.
The ISO/IEC 27001:2022 standard defines 93 controls grouped in Annex A, covering areas like people, technology, and processes. These are documented in your Statement of Applicability (SoA), which shows which controls you’ve chosen, why, and what evidence supports them.
This guide explains how the controls work, what auditors look for, and how to prepare for audit success.
Understanding ISO 27001
ISO 27001 is an international standard for managing information security, developed by the International Organisation for Standardisation (ISO) and the International Electrotechnical Commission (IEC). First published in 2005, revised in 2013, and updated in 2022, it helps organisations identify risks, apply appropriate controls, and systematically protect sensitive information.
What are ISO 27001 controls?
ISO 27001 controls are safeguards that reduce information security risk. They are practical measures you put in place to protect your data and systems from threats, such as cyber attacks, human error, or misuse.
Under ISO/IEC 27001:2022, there are 93 controls, grouped into 4 themes:
Organisational controls - Policies, roles, supplier management, incident response.
People controls - Screening, training, awareness, disciplinary processes.
Physical controls - Secure offices, access badges, equipment protection.
Technological controls - Access control, encryption, monitoring, secure development.
Together, these controls protect the 3 core principles of information security:
Confidentiality - Only authorised people can access information.
Integrity - Information remains accurate and complete.
Availability - Information is accessible when needed.
However, you do not automatically implement all 93 controls. Each control must be selected based on your risk assessment, not because it simply appears in Annex A.
Annex A vs Clauses 4-10
This is where many organisations get confused.
ISO 27001 contains two key parts:
Clauses 4-10 - These define the management system requirements.
Annex A - This provides the control catalogue (93 controls).
In simple terms:
Clauses = What you must have in place to run your ISMS.
Annex A = Possible controls you may use to treat identified risks.
Clauses 4-10 are mandatory requirements. Every certified organisation must meet them. They cover areas such as leadership, planning, support, operations, performance evaluation, and continual improvement.
Annex A controls, on the other hand, are not automatically mandatory. You must:
Identify risks through a formal risk assessment
Select appropriate controls to reduce those risks
Justify your decisions in your Statement of Applicability (SoA)
If you exclude a control, you must explain why. Auditors will always review your SoA to ensure your control selection is logical, risk-based, and supported by evidence.
This distinction is critical for audit readiness. Many certification delays happen because organisations focus heavily on policies, but fail to clearly connect risk → control → SoA justification.
How many ISO 27001 controls are there?
Under ISO/IEC 27001:2022, there are 93 controls listed in Annex A, which in turn are taken from the controls listed in ISO 27002.
In the previous 2013 version, there were 114 controls.
The 2022 update did not weaken the standard. Instead:
Controls were restructured and streamlined
Several were combined for clarity
11 new controls were introduced to reflect current security challenges
So while the number reduced from 114 to 93, the overall level of protection did not decrease. In fact, the structure is now more practical and easier to audit.
ISO 27001:2022 control breakdown
The 93 controls are grouped into 4 themes:
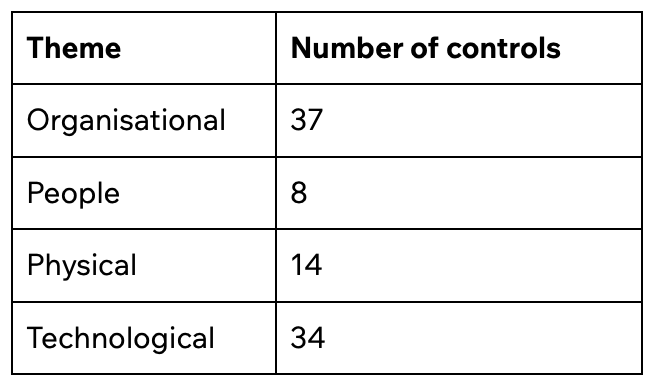
This structure replaces the old 14-domain model from ISO 27001:2013 and makes control ownership clearer, particularly for SMEs and SaaS organisations.
From an audit perspective, the number itself matters less than how well your selected controls map to your risks and your Statement of Applicability. Auditors are not checking whether you implemented 93 controls. They are checking whether you implemented the right controls for your organisation.
Are organisations still mixing up the 2013 and 2022 versions?
This is no longer a live issue. The formal transition period has closed, and all certified organisations must now meet ISO 27001:2022. New certifications are only assessed against the 2022 version.
Although Annex A was reorganised and reduced from 114 to 93 controls, the core clauses and overall structure of the standard remain largely consistent. Even during the transition period, confusion was limited. Where it did occur, it was usually due to older 2013-based templates referencing outdated control numbers, which auditors could quickly identify and correct.
The 4 themes of ISO 27001 controls [2022 structure]
The 2022 update reorganised Annex A into 4 clear themes: Organisational, People, Physical, and Technological.
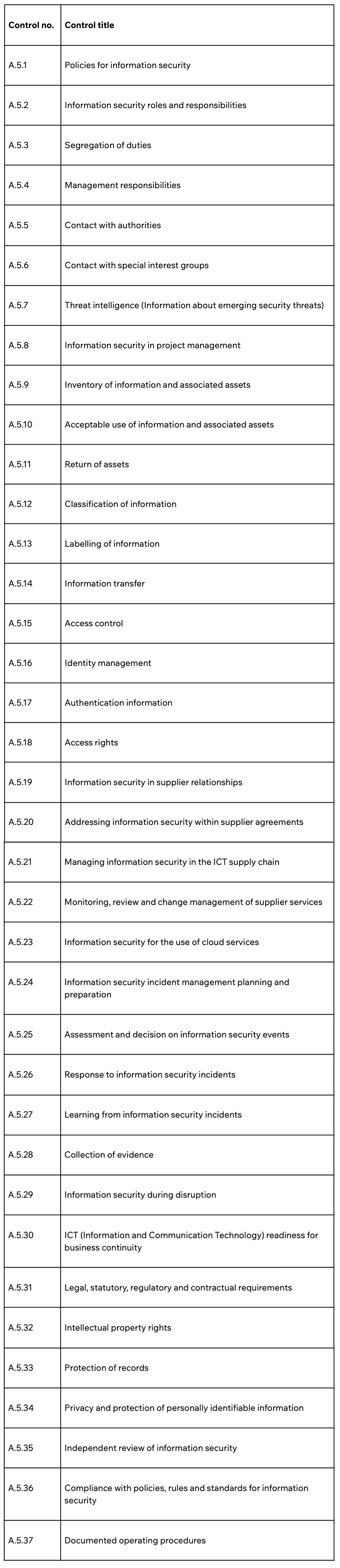
Organisational controls (A.5 - 37 controls)
These controls focus on governance and oversight. They set the foundation for how information security is managed across the organisation.
They cover:
Governance and policy
Risk management
Supplier management
Incident management
Business continuity
Legal and regulatory compliance
From an audit perspective, this section often determines whether your ISMS feels structured or informal.
Auditors typically check:
Are policies documented, version-controlled, and formally approved?
Are roles and responsibilities clearly assigned?
Is supplier risk assessed and reviewed regularly?
Is there evidence of independent management review?
Annex A.5 – Organisational controls list
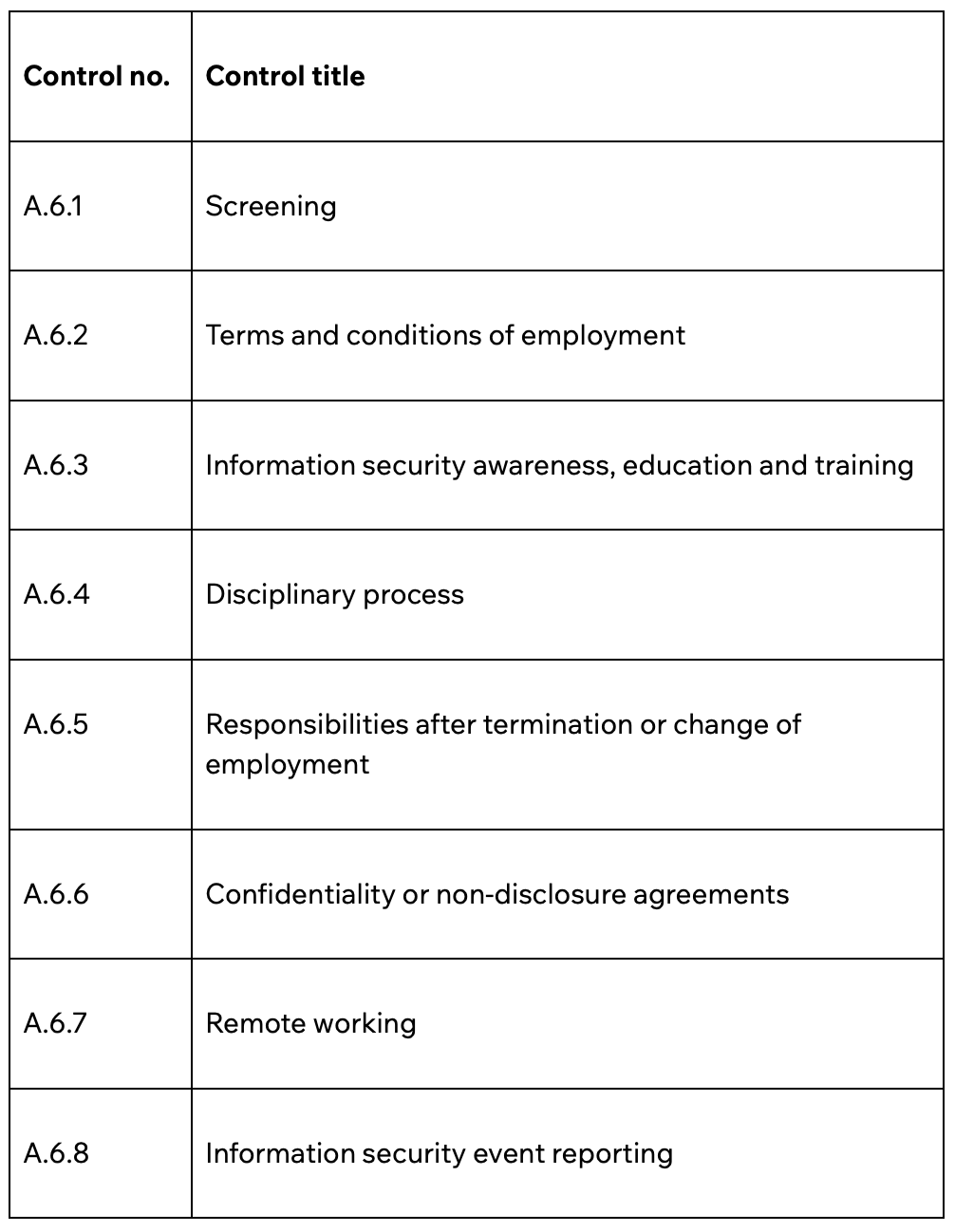
People controls (A.6 - 8 controls)
People remain one of the largest sources of risk. These controls ensure that employees and contractors understand their responsibilities and behave securely.
They focus on:
Background screening
Contracts and NDAs
Ongoing awareness training
Remote working security
Secure termination and role changes
Audit evidence usually includes:
Training logs and attendance records
Signed employment contracts and NDAs
Offboarding checklists
Clear incident reporting mechanisms
A common gap is treating awareness training as a one-off exercise rather than an ongoing programme.
Annex A.6 – People controls list
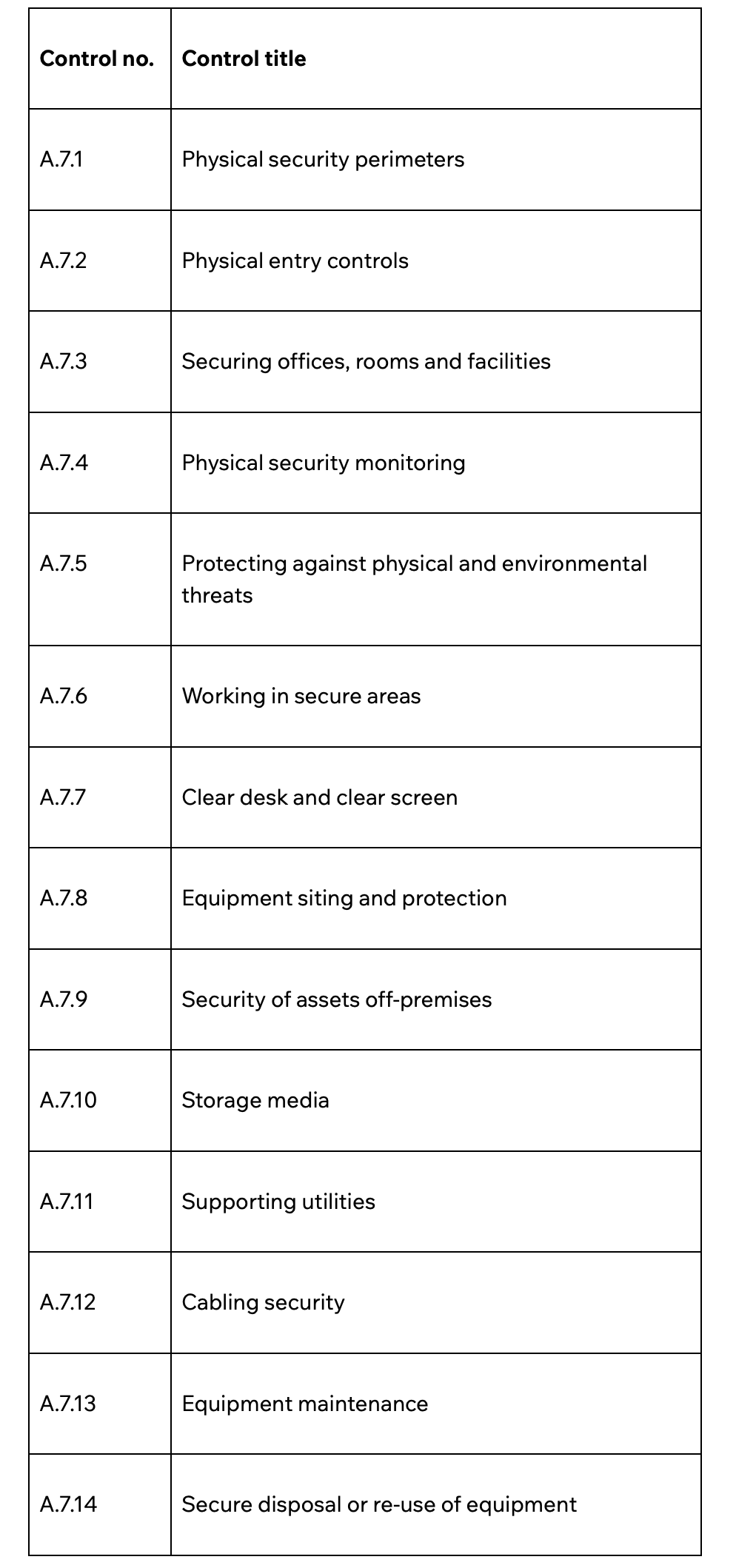
Physical controls (A.7 - 14 controls)
Physical controls protect offices, facilities, and equipment from unauthorised access or damage.
They focus on:
Entry controls and visitor management
Secure areas
Equipment protection
Clear desk and clear screen practices
Secure disposal of assets
Auditors often review:
Office access logs
CCTV coverage
Evidence of laptop encryption
Asset disposal certificates
A common SME issue is that physical controls exist informally but are not documented or consistently applied.
Annex A.7 - Physical controls list
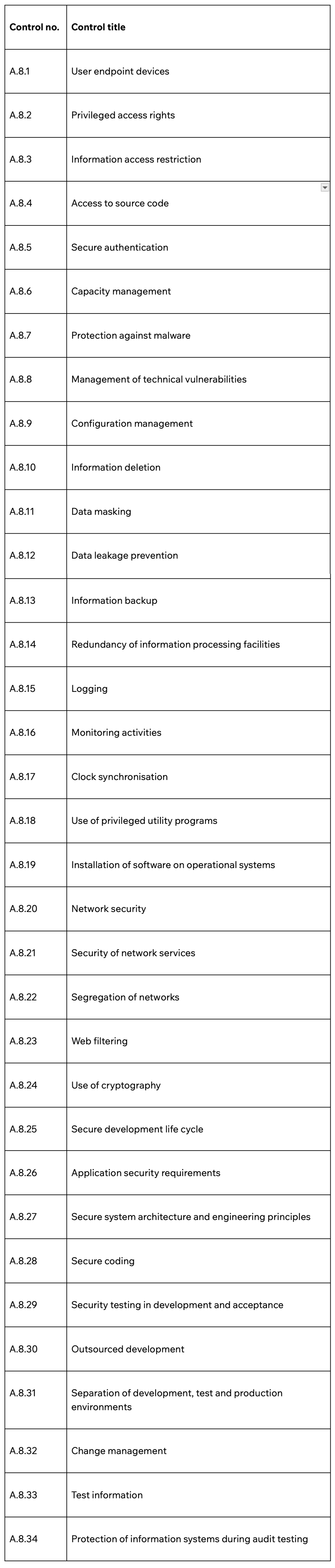
Technological controls (A.8 - 34 controls)
These controls address technical safeguards across networks, systems, applications, and data.
They focus on:
Access control and privileged access
Malware protection
Logging and monitoring
Backup management
Encryption
Secure development
Change management
Vulnerability management
Auditors expect to see:
Documented change control procedures
Evidence that backups are tested
Vulnerability scanning and patch reports
Privileged access reviews
Logging that is reviewed, not just enabled
A frequent nonconformity is having system logs switched on but never reviewed or analysed.
Annex A.8 - Technological controls list
How to apply ISO 27001 controls in practice
Understanding the 93 ISO 27001 controls is one thing. Applying them properly is what determines whether you pass the audit with confidence.
Implementation should always follow a clear, risk-based path. When that structure is missing, controls often exist on paper but not in practice.

1. Conduct a risk assessment
Everything starts with risk.
You first identify:
Your information assets (data, systems, people, suppliers)
Relevant threats (phishing, insider misuse, system failure, supplier breach)
Existing vulnerabilities
The impact and likelihood of each risk
This process explains why you need certain controls. Without it, control selection becomes arbitrary, which auditors will quickly challenge.
Related read -
2. Map risks to Annex A controls
Once risks are defined, you select controls that reduce them to an acceptable level.
For example:
Risk: Phishing attack leading to account compromise
Relevant controls might include:
Awareness training (People control)
Multi-factor authentication (Technological control)
Logging and monitoring (Technological control)
Incident response procedures (Organisational control)
This mapping demonstrates that controls are chosen intentionally, not copied from a template.
Auditors will often ask: “Show me which risk this control addresses.”
If you cannot answer clearly, your SoA is likely weak.
3. Document in the Statement of Applicability (SoA)
The Statement of Applicability is where everything comes together.
It should clearly show:
Which Annex A controls are included
Which controls are excluded
The justification for each decision
The implementation status of each control
Exclusions are allowed. However, they must be logically justified. Simply stating “not applicable” without explanation is a common audit finding.
A strong SoA makes the audit structured and predictable. A vague SoA invites deeper scrutiny.
4. Implement and embed the controls
This is where many organisations underestimate the effort required.
Implementation means:
Updating and approving policies
Assigning clear ownership
Training staff
Embedding processes into daily operations
Monitoring performance
Conducting internal audits
Reviewing at the management level
A control is only effective if it operates consistently over time.
Control ownership: Who is responsible for implementing the controls?
A common misconception is that ISO 27001 controls are owned by IT. In reality, information security is cross-functional. Controls sit across the organisation, and responsibility must reflect that.
For example
HR is typically responsible for screening, employment terms, NDAs, awareness training, and offboarding processes.
Legal or compliance oversees regulatory obligations, contractual requirements, and privacy controls.
Facilities or operations manage physical security, access controls, CCTV, and secure disposal.
IT or engineering handle access management, logging, backups, secure development, and vulnerability management.
Leadership owns governance, risk acceptance decisions, resource allocation, and management review.
When ownership is unclear, tasks are delayed, reviews are missed, and audit findings become more likely.
How auditors distinguish real accountability from paper responsibility
One of the strongest indicators of ISMS maturity is whether control ownership is genuine or merely documented. Auditors can usually identify the difference quickly because real ownership leaves a clear evidential trail.
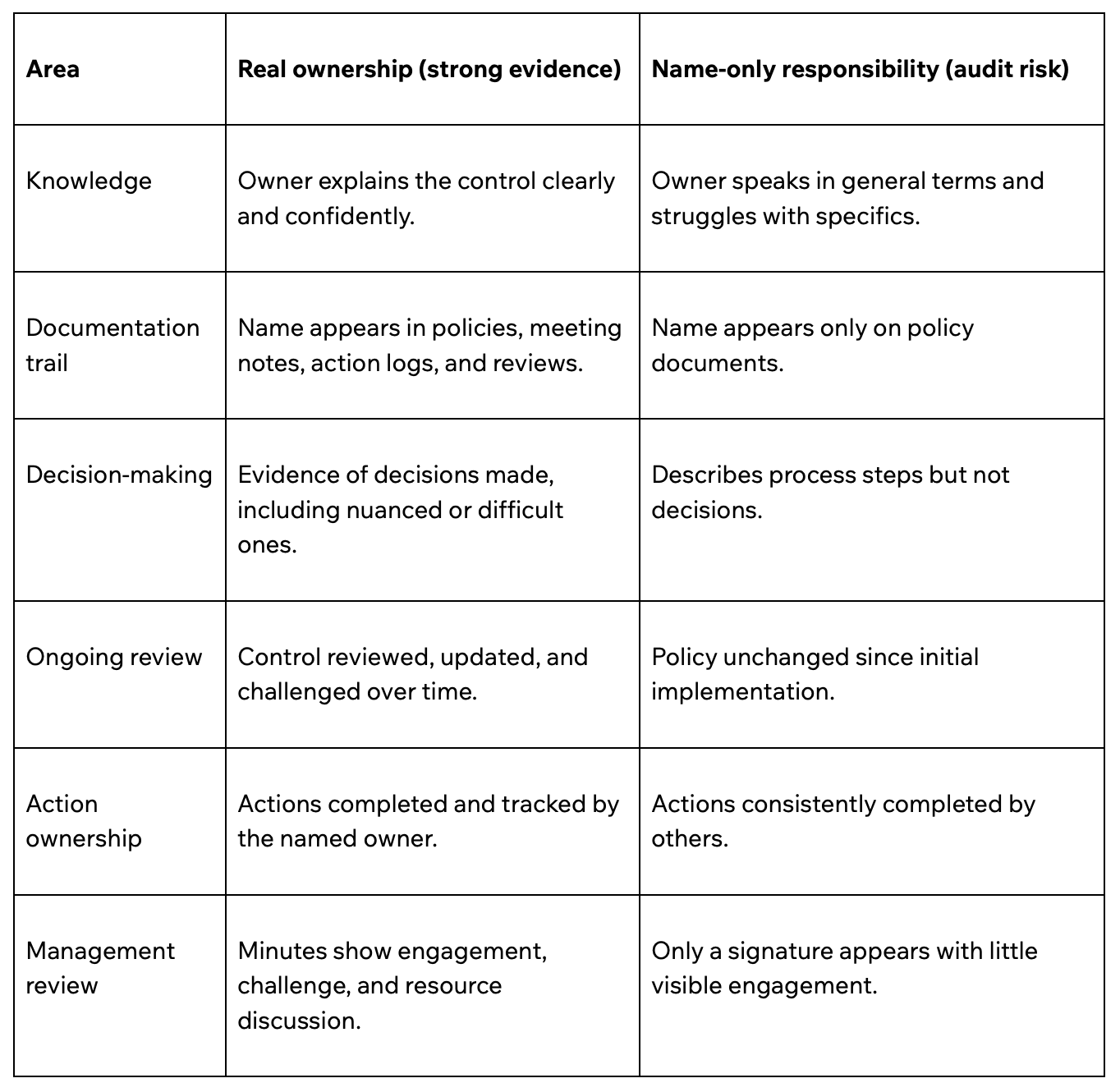
Auditors often test ownership through scenario-based questions. Genuine owners respond with judgment and decisions. Nominal owners tend to repeat documented procedures.
Auditor insight: Controls that look simple but require ongoing operational effort
Several ISO 27001 controls appear straightforward at implementation, but require sustained operational time.
Access reviews - Writing an access policy is quick. Running documented, periodic access reviews across every system - and evidencing changes - is not. In growing organisations, this becomes a recurring commitment.
Asset management - Keeping your asset register accurate as devices, cloud resources, and licences change requires discipline or tooling. Registers often drift over time.
Supplier reviews - Having a supplier policy can be simple. Conducting and documenting meaningful security reviews of key suppliers regularly is resource-intensive, particularly where third parties are slow to provide evidence.
Training and awareness - Delivering annual training is manageable. Demonstrating that it is current, relevant, and effective - not just completed - requires engagement tracking and follow-up.
Common ISO 27001 control failures in audits
Access control (A.8.2 / A.8.3) is one of the most common failure areas. Organisations often have a policy, but leavers retain access, privileged rights are too widely distributed, and formal access reviews are either not performed or not evidenced.
Supplier security (A.5.19 / A.5.20) is another frequent gap. A supplier register may exist, yet there is little evidence of security assessments, contractual review, or ongoing monitoring.
In incident management (A.5.24–A.5.28), policies are in place, but incident logs lack detail, root cause analysis, or documented learning.
With cryptography (A.8.24), encryption is implemented, but key management responsibilities and rotation processes are unclear.
For vulnerability management (A.8.8), patching policies exist, yet there is limited evidence of scanning, remediation tracking, or review.
Auditors ultimately look for consistent, documented operation over time, not one-off implementation activity.
How ISO 27001 controls are assessed in certification audits
Understanding the controls is important.
Understanding how they are assessed in a certification audit is no less.
A common question is whether an ISO 27001 audit must be conducted on-site. The answer depends on whether a remote approach can deliver the same level of assurance as a physical visit.
The key consideration is whether the organisation operates critical physical infrastructure, such as server rooms, on-premise hardware, or secure storage, that genuinely requires in-person inspection. Where such infrastructure exists, on-site audit activity is typically required for those elements.
For many clients of Tempo Audits, particularly cloud-native technology businesses, there is no significant on-premise infrastructure. In those cases, audits are conducted entirely remotely because that reflects the organisation’s actual risk profile and control environment.
Remote assessment does not mean physical controls are accepted without scrutiny. Auditors gather robust evidence through live video walkthroughs of offices or secure areas, photographic confirmation of access controls and clean desk practices, and review of access logs, visitor records, CCTV policies, and physical security risk assessments.
Whether remote or on-site, the objective remains the same: to verify that ISO 27001 controls are operating effectively, proportionately, and in line with the organisation’s real-world risk exposure.
Ready to certify with confidence?
If you are preparing for ISO 27001 certification and want clarity on how your controls will stand up to audit scrutiny, speak to Tempo Audits. Request a quote to receive a clear, transparent proposal and understand what your certification journey will involve.
FAQs
-
No. ISO 27001 is risk-based, not checklist-based. Small businesses do not automatically implement all 93 controls. Instead, controls are selected based on identified risks and justified in the Statement of Applicability.
-
Auditors look for proof that controls operate consistently over time. This typically includes access review records, vulnerability scan reports, supplier assessments, incident logs, training records, management review minutes, and documented decisions.
-
Implementation timelines vary depending on organisational size, complexity, and existing maturity. For SMEs with defined processes, implementation typically takes 3-6 months. Larger or more complex organisations may take longer.
